Keeping track of Infrastructure as Code (IaC) versions across multiple repositories can be a challenge.
With different teams using different versions of Terraform, Terragrunt, or OpenTofu, keeping track of compliant and vetted modules while ensuring alignment within the team becomes a burden.
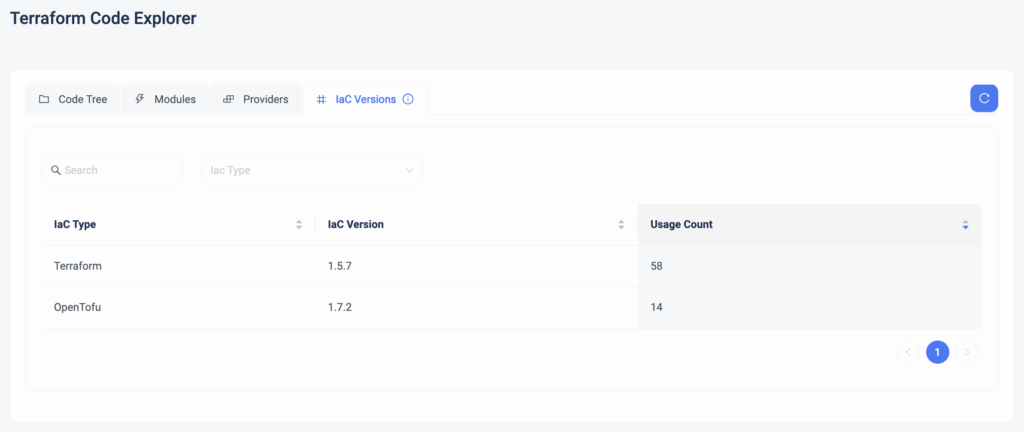
Today, we are happy to announce the release of IaC Versions Explorer, the single source of truth for all your IaC versions.
This means:
- See it all in one place: Instantly view all Terraform, Terragrunt, and OpenTofu versions in use across your stacks.
- Prevent version drift: Identify outdated or unapproved versions.
- Standardize across teams: Ensure everyone uses the correct versions, reducing compatibility issues.
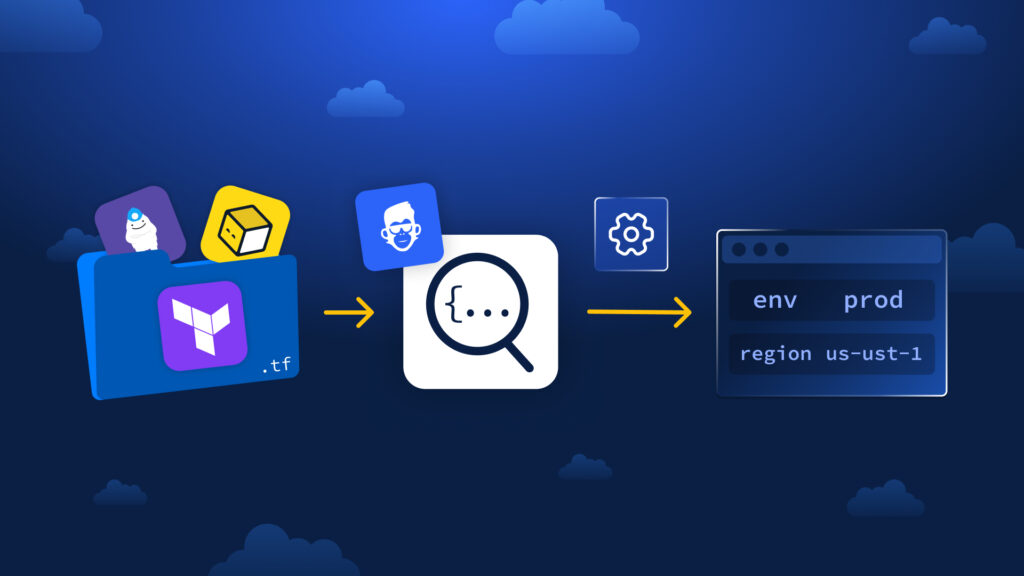
How It Works
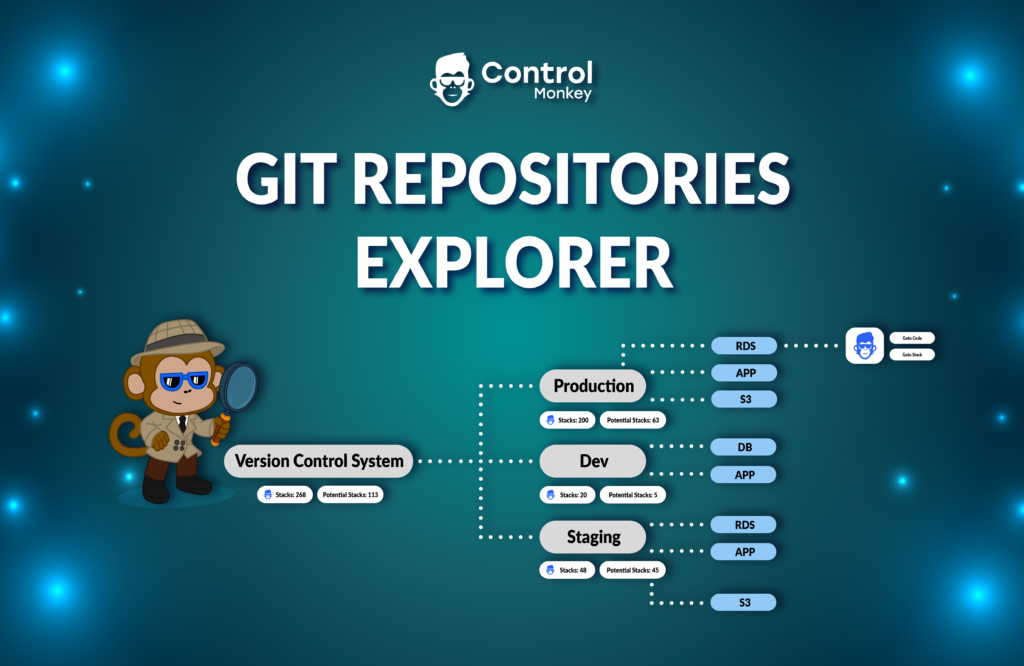
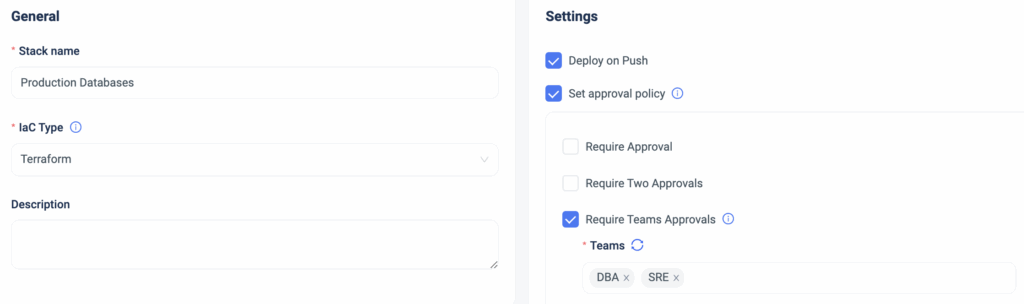
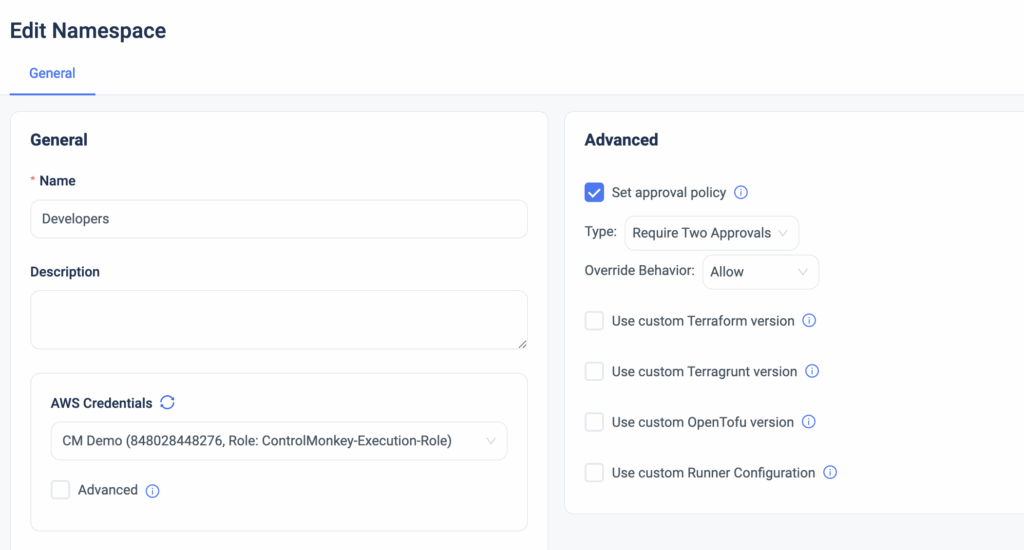
The IaC Versions Explorer gives you a real-time view of all the Terraform and OpenTofu versions running in your environment. With just a few clicks, you can:
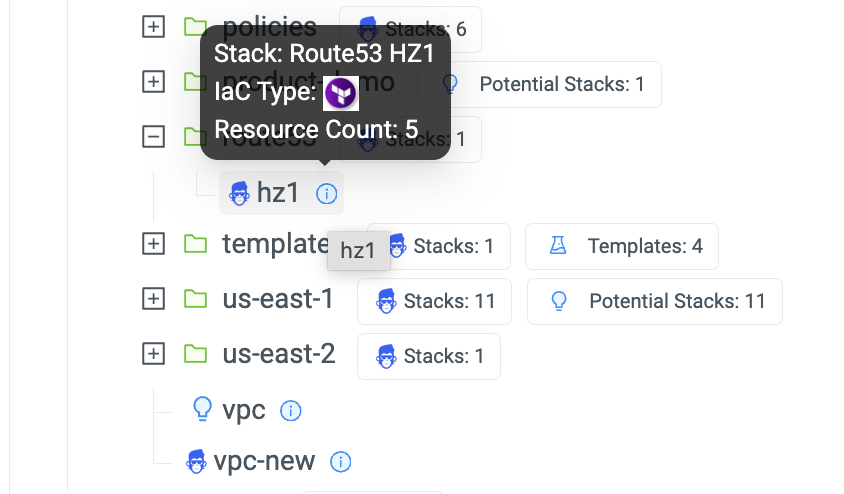
- See a full breakdown of the IaC versions in use.
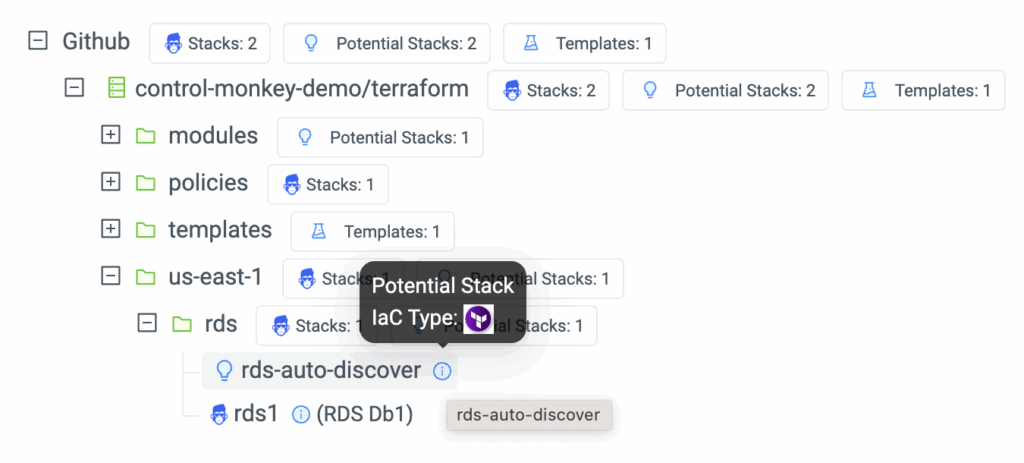
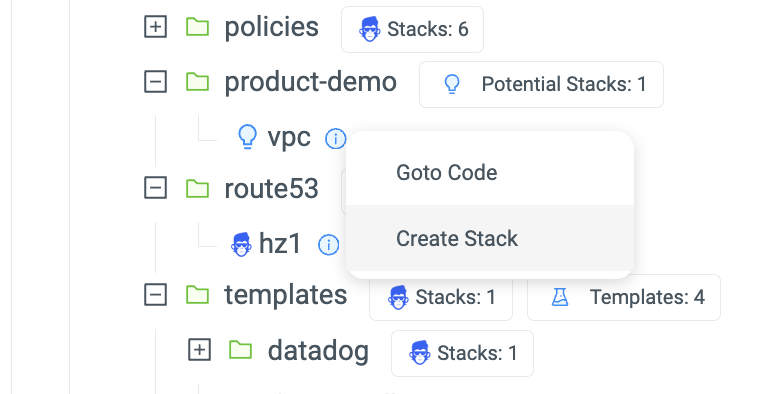
- Drill down into each version to check where it’s deployed across namespaces and stacks.
- Catch outdated versions early and ensure consistency across all teams.
ControlMonkey helps eliminate uncertainty and keeps your IaC environments consistent by giving you complete visibility and Control.
No more misaligned versions
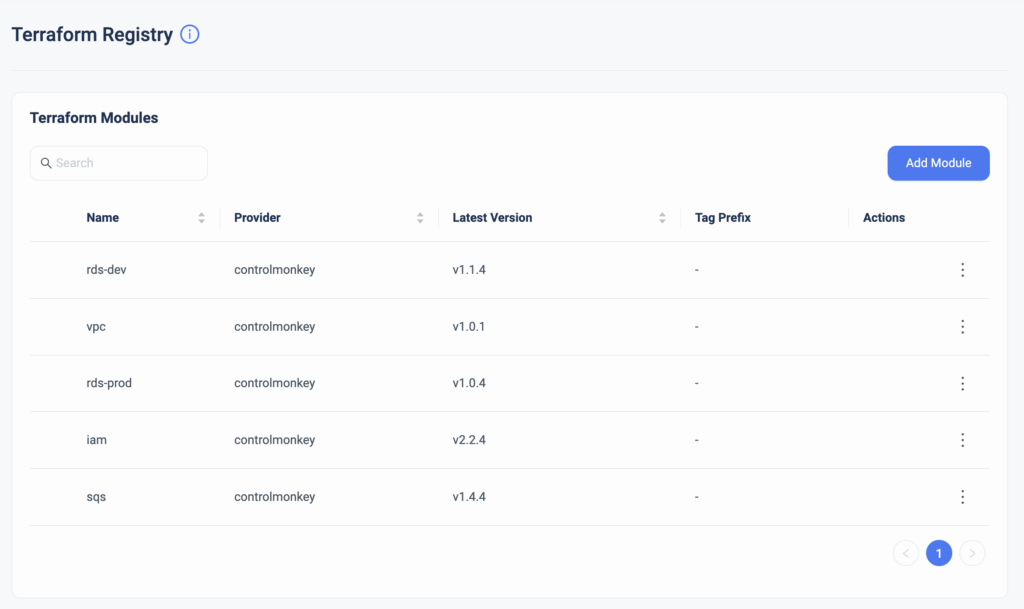
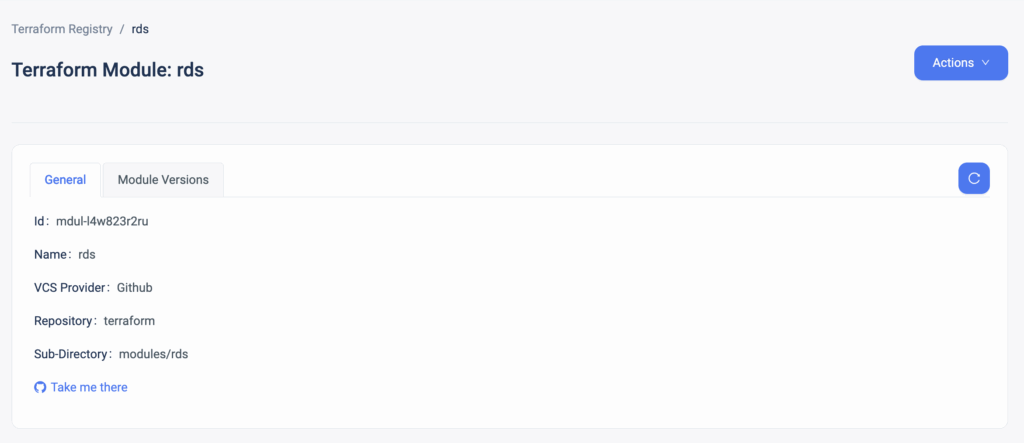
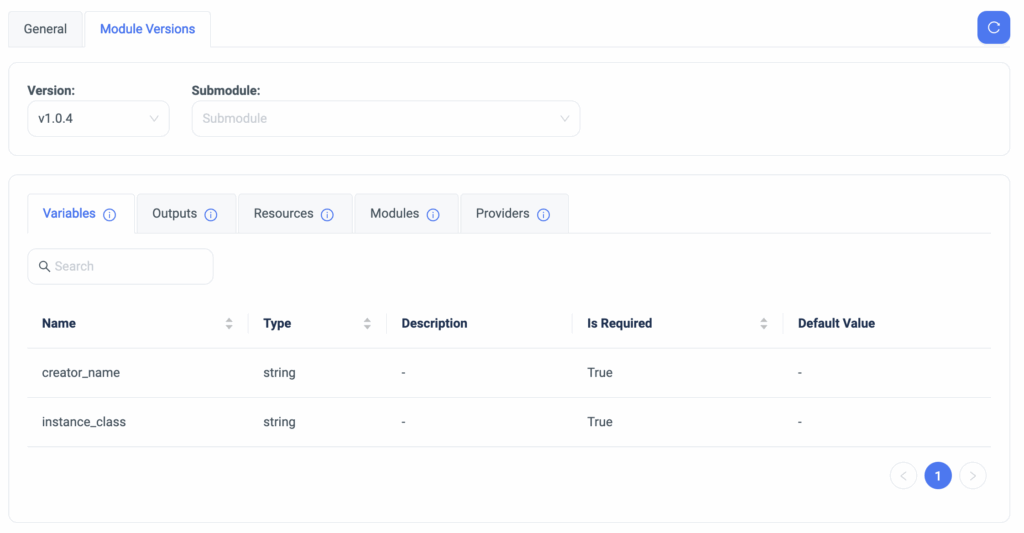
ControlMonkey’s Terraform Knowledge Hub solution provides all the tools to visualize and control your Terraform modules, providers, IaC versions, and repositories on a single platform.
Ready to take control of your infrastructure?
Meet with our Terraform experts for a 30-minute technical call to learn more.