IaC modernization sits at the core of scalable, secure, and resilient cloud operations. The fact is, the way most organizations traditionally design their IaC is being rendered outdated quickly. IaC allows teams to describe their infrastructure using code so that they can version, review, and deploy it just like application code.
This helps reduce manual work and human errors. However, with expansion, organizations encounter new challenges. The same scripts that proved desirable with smaller teams become hard to maintain, hard to version-lock, and risky among large groups that work together. The new requirements, including security and compliance rules, as well as the newer code assisted by AI, enable teams to work faster and more safely with more specific controls and improved workflows.
That’s why infrastructure as code must always be kept up to date and current. New IaC is more than just generating templates; it’s done with the correct structure, an efficient process, tight security, and intelligent automation. This ensures that your cloud remains stable and secure as it scales.
Why IaC Modernization Matters Now
Infrastructure as Code revolutionized the way teams provision and handle cloud infrastructure. It replaced manual processes with reusable, versioned code. This helps teams spin up new environments fast and reliably. Today, organizations operate at an entirely different scale. They have dozens or hundreds of cloud accounts, complex infrastructures, and several teams that have access to the IaC code. Rules and security must conform to higher requirements, unlike before. Tiny flaws in legacy scripts trigger outages or data leaks.
Modern teams want to automatically review and verify all changes before they go live. They want the ability to manage secrets, passwords, and access keys. They want to know who changed what and when. The higher the number of code generation utilities, the higher the necessity to implement controls. Although AI accelerates template generation, it also produces unsafe configurations unless strict rules validate every change.
That is why IaC modernization is needed today. It provides teams with better ways to handle growth, maintain secure infrastructure, and move faster without losing control.
Pillars of Modern IaC: What to Focus
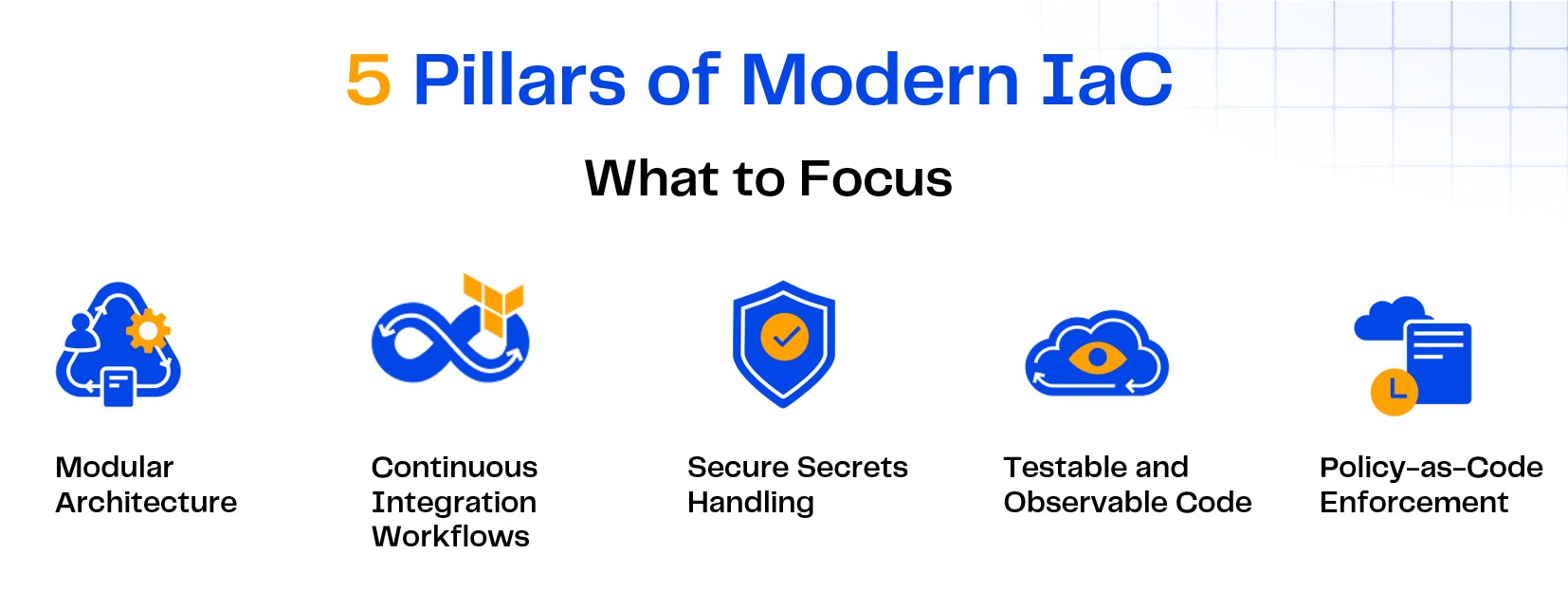
Modern IaC is not just about writing templates. Best practice is to design infrastructure to be reusable and manageable, and where feasible deploy it immutably by creating new resources and retiring old ones. The five most important focus areas when modernize Infrastructure as Code are:
1. Modular Architecture is key for IaC Modernization
IaC modernization should be modular. Rather than having one large file with the whole thing, divide your infrastructure into small, reusable building blocks, or modules. The modules are versionable and testable. This makes it easy for multiple teams to share them without breaking each other’s work. Updating one module should not affect other parts unless you want it to.
For example, an organization may maintain its common library of approved network modules, security groups, and IAM roles. All the teams reuse such modules while developing new projects. This reduces the effort and time.
2. Continuous Integration Workflows
Treat infrastructure code just as you would treat application code. All changes should be subject to a pull request, code review, and automated checks.Pipelines should run terraform plan, syntax checkers, security scanners, and policy validations. This stops unsafe changes from reaching production. When teams work this way, they do not need to remember every best practice; the pipeline does it for them.
For example, static policy checks in the CI/CD pipeline (e.g., OPA or Sentinel) can block any configuration that would allow SSH access to the public internet before Terraform is applied. It prevents newly employed engineers from making mistakes and maintains top-notch security without inconveniencing individuals.
3. Secure Secrets Handling
In older setups, people often hardcoded secrets, such as AWS keys or database passwords, in plain text. This is dangerous and can lead to leaks. IaC modernization relies on dedicated secrets-management services whether a cloud-native offering such as AWS Secrets Manager or a self-hosted vault solution.
Never store secrets in Terraform files or Git repositories. They are injected at runtime ideally mounted as temporary files (or pulled directly into memory on serverless runners without a writable file system) or fetched by a secrets agent rather than exposed in environment variables. This keeps sensitive data under control and facilitates easier audits.
4. Testable and Observable Code
IaC modernization should be testable. Use tools that check your code before you apply it. Tools like ‘tflint’ or ‘terraform validate’ catch mistakes early. For more advanced checks, tools like Checkov or Terraform-compliance help ensure your code meets security rules.
Drift detection is also essential. Drift occurs when engineers change resources in the console rather than through code. Modern setups may combine a managed SaaS backend (e.g., a Terraform-compatible cloud service), open-source drift-detection plugins such as driftctl, or configuration-compliance services like AWS Config to find these changes automatically. This helps teams keep their environments under control.
5. Policy-as-Code Enforcement
Policy-as-Code codifies the rules that keep infrastructure aligned with company standards. For example, you can enforce that all S3 buckets are encrypted, require MFA when users assume sensitive IAM roles, or ensure only approved AMIs are used.
General-purpose policy engines such as Open Policy Agent (OPA) or policy-as-code languages built into IaC platforms can enforce these checks in your pipelines, while AWS Control Tower guardrails provide managed SCPs and Config rules that complement them. The pipeline automatically blocks non-compliant changes.
This reduces mistakes, keeps teams compliant, and saves time on manual reviews.
Enabling IaC Modernization – Workflows, Automation, and Tooling.
IaC modernization is not only about writing good code. It also depends on strong workflows, intelligent automation, and the right tools. This section explains how teams can connect everything so that infrastructure changes are safe, repeatable, and easy to manage at any scale.
1. Starting with Intelligent Pipelines
A contemporary IaC pipeline does far more than terraform plan and terraform apply. It integrates with your CI/CD tool to execute checks automatically whenever someone is proposing a change. Pipelines include approval steps for large updates, static code checks to find bugs, secure handling of secrets, and policy checks to define standards. Pipelines also audit all plans and apply steps, which simplifies both debugging and auditing. By combining these steps, teams can deploy infrastructure changes more quickly and with greater confidence.
2. Adopt GitOps for Infrastructure
GitOps means your Git repository is the single source of truth for your infrastructure. If it’s not in Git, it does not exist. Any change must go through Git pull requests and pipelines. This prevents people from making manual changes in the cloud console that cause confusion or break systems. Tools like Argo CD and Flux bring the GitOps approach to Kubernetes, and can integrate with Terraform or other IaC through plugins when you need to manage non-Kubernetes resources.
3. Adding Drift Detection
Even with GitOps, sometimes people make emergency changes in the console. Drift detection tools compare your current cloud state to what is in your code. If something does not match, you get an alert or an automatic fix. This keeps your environments consistent and reduces surprises during audits.
4. Use Proven Tooling
IaC modernization does not mean you need to build everything from scratch. Utilize mature open-source modules, community registries, and industry standards. Take Terraform, for example, with the Terraform Registry, where hundreds of teams use tried-and-trusted modules. This helps you build faster.
Driving Change – Strategic Leadership for Sustainable IaC
IaC modernization goes beyond tools; leaders must embed best practices and drive cross-team collaboration. Below are key focus areas for leaders who want to build sustainable IaC practices.
- Define Clear Standards: Leaders must set strict rules of how IaC is encoded, reviewed, and propagated. These include naming conventions, tagging, folder structure, and module versioning. Standards help different teams work together consistently, even as the organization expands.
- Invest in Reusable Building Blocks: A good leadership strategy is to support teams with ready-to-use, well-tested modules. Network modules that can be reused, IAM role templates, or logging configurations enable teams to quickly and securely spin up new environments with minimal or no ground-up work each time.
- Automate Governance: Manual checks do not scale. This requires automation for security and compliance. This means building policy checks, drift detection, and approval gates into pipelines. Automated governance protects the organisation without stalling teams.
- Enable Continuous Learning: IaC best practices keep evolving. There should be time set aside for teams to get new tools, share lessons learned, and work together to refine modules as a team. This could be through workshops, code reviews, or regular knowledge-sharing sessions.
- Build a Culture of Shared Responsibility: Modernize infrastructure as code works best when everyone takes ownership, and leaders should encourage teams to contribute back improvements, fix modules, and follow best practices as part of daily work, not just special projects.
- Plan for Long-Term Growth: Good leadership sees modernize infrastructure as code as an ongoing investment rather than an initial upgrade. They will again study tools and workflows, update policies accordingly, and support future needs such as AI-assisted code or multi-cloud platforms.
IaC Modernization – Building for Speed, Safety, and AI-Readiness
Organizations that modernize infrastructure as code don’t merely write better scripts, they create a cloud foundation built for speed, security, and AI-readiness. It’s about creating an environment where teams can build, and grow cloud resources with confidence. Clear standards, reusable modules, secure pipelines, policy checks, and drift detection all help reduce mistakes. With good and accurate modules, secure secrets, and automated pipelines, your infrastructure remains reliable, even as AI tools begin to assist in writing more of it. Strong leadership makes this possible by guiding teams, removing barriers, and supporting good tools and training. A tool such as ControlMonkey makes IaC modernization easier.





