Cloud compliance starts with visibility—but it’s sustained by governance. A Cloud Governance Framework defines how your cloud resources are designed, deployed, and monitored in alignment with compliance requirements. It turns security policies into operational rules, helping organizations avoid regulatory drift and scale securely.
Here’s what a cloud governance framework includes—and how to build one that balances innovation with control
🛡️ Explore Cloud Compliance & Governance:
- 🌐 What Is Cloud Compliance?: A foundational guide to cloud regulations and governance frameworks.
- 🇪🇺 NIS2 Compliance: Automate critical infrastructure standards across the EU.
- 🩺 HIPAA Compliance: Secure PHI in cloud-native environments.
- 🏛️ FedRAMP Readiness: Meet U.S. federal cloud standards with IaC automation.
- 💳 PCI DSS 4.0 Compliance: Align DevOps workflows with cardholder data regulations.
Laying the Foundations for a Cloud Governance Framework
Essentially a blueprint for best practice and operational discipline, a Cloud Governance Framework is a structured set of rules, policies, roles, and processes that guide the organization on how cloud resources are managed across the business. This avoids compliance risks being handled reactively and only being addressed during times of audit and/or incidents.
Businesses often look at governance as a burden, but when it is done well—and supported by the right automation tools—it streamlines compliance work by eliminating duplicated effort and reducing the risk of mistakes. This leads to a more secure, scalable and reliable cloud infrastructure.
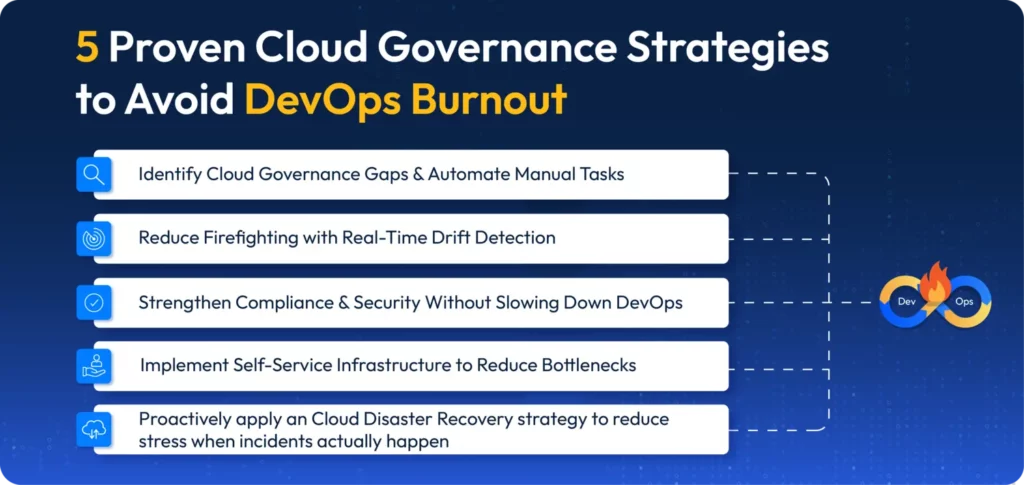
The Four Key Pillars of a Cloud Governance Framework
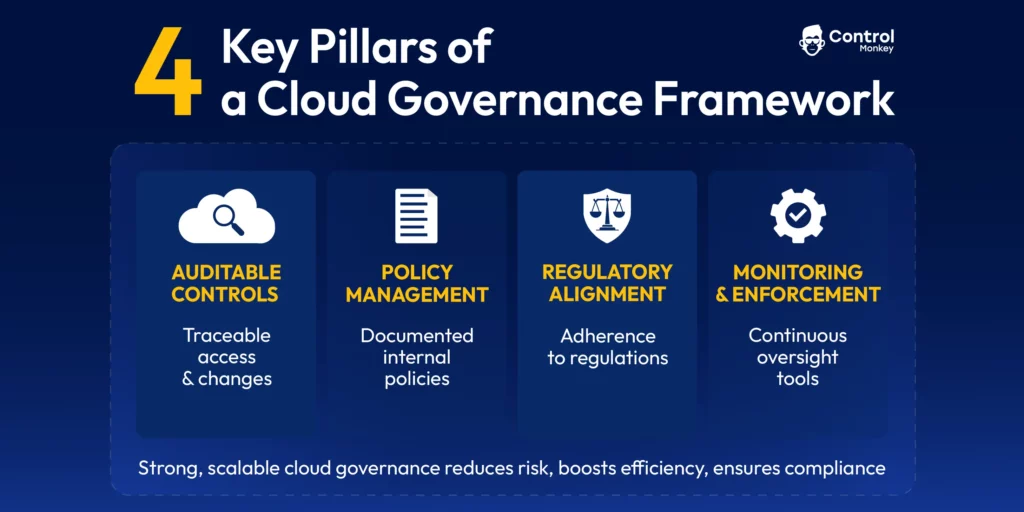
A well-implemented cloud governance framework should contain four key pillars:
Auditable cloud controls for traceability:
Having specific controls in place ensures that there is a mechanism for tracking activities such as system access, infrastructure changes, and policy implementation. These controls should be monitored by audit and compliance teams so they can provide assurance that the cloud environment is being managed in accordance with the regulations and best practices adopted by the business.
Robust policy management:
The organization’s internal policies on cost, security, data residency should be documented and implemented within the framework.
Regulatory compliance alignment:
The far-reaching requirements of the many regulations the organization must meet should be collated and rationalized within the framework, so duplicated work is avoided.
Rigorous cloud governance monitoring and enforcement tools:
Governance means ensuring the processes, roles and responsibilities outlined in the framework are effectively delivered. This makes monitoring and enforcement an integral part of the process that should be enabled with automation as far as possible.
A strong, scalable cloud governance framework reduces business risk, increases efficiency and productivity and cuts costs, while ensuring continuous compliance. Of course, every organization will need to adapt the framework to their needs, their cloud maturity and the regulations they need to adhere to. They must also ensure they devote the right level of resources to developing and maintaining cloud governance.
Implementing a Cloud Governance Framework: Essential Tools and Best Practice
Within the four pillars above there are a number of practical steps to take and technologies to deploy, including:
1. Identity and Access Management (IAM)
- Implement least-privilege access to minimize breach risk.
- Use role-based access controls (RBAC) to prevent over-permissive access or privilege escalation.
- Enforce MFA and SSO policies.
You can address IAM risk and block IAM violations by enforcing pre-merge checks and RBAC policy templates. Tool such as OPA Rego Policies, tfsec and Terraform AWS IAM modules can help deliver robust IAM and control.
2. Resource Visibility and Tagging
- Define mandatory tagging standards (e.g., owner, environment, cost center)
- Use automated enforcement via IaC or policy-as-code tools such as ControlMonkey Quality Gates, Open Policy Agent or HashiCorp Sentinel
3. Cloud Cost Management and Optimization
- Set budgets and alerts to avoid overspend.
- Enforce resource lifecycle policies.
- Use anomaly detection to identify spikes.
You can use native cloud cost management tools or third party cloud cost optimization options, but whichever you choose you must configure it to match your internal policies.
4.Cloud Security and Compliance Policies
- Define guardrails for encryption, firewall rules, data egress.
- Implement continuous compliance scanning.
Standards such as NIST SP 800 and ISO/IEC 27001offer prescriptive guidance for information management, data security and privacy controls and should be fully integrated into policies and operations via the cloud governance framework.
5. Change Management and Automation
- Use Infrastructure as Code (IaC) tools like Terraform to enforce reproducible infrastructure.
- Integrate quality gates and enforce infrastructure tagging and approval workflows to ensure infrastructure is always compliant.
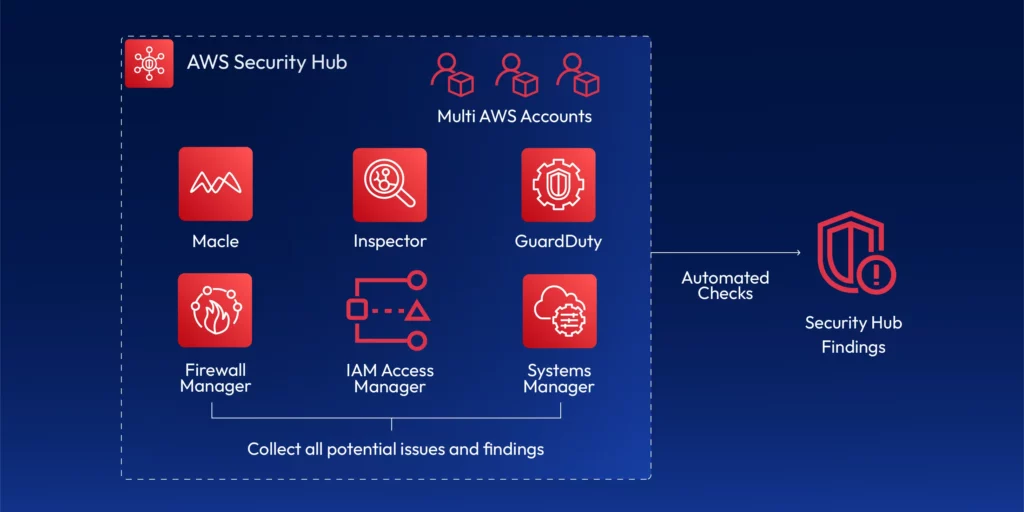
6. Monitoring and Incident Response
- Centralize logging and alerts using tools like Terraform Plan Logs or
AWS CloudTrail. - Set up SLA-driven escalation procedures.
Infrastructure as Code (IaC): Enabling Cloud Governance Enforcement at Scale
Infrastructure as Code (IaC) sits at the heart of the work DevOps need to do to maintain cloud compliance within a cloud governance framework. It delivers infrastructure safely and securely and enables DevOps to:
- Automate compliance checks before deployment
- Maintain oversight and monitor for misconfigurations and drift.
- Self-service IaC enables standardized compliance and fast infrastructure provisioning avoiding bottlenecks.
- You can track and audit changes, so you don’t break cloud governance
Platforms like ControlMonkey support the delivery of a strong cloud governance framework by offering automated enforcement, policy-as-code capabilities, and real-time visibility into cloud misconfigurations. IaC transforms compliance from a reactive audit tick box exercise to enabling DevOps to provide fast, compliant, standardized IaC delivery for the business.
A strong cloud governance framework does more than just provide control, stability, and risk mitigation—it fuels innovation, optimizes cloud efficiency, accelerates return on investment, and gives your business a true competitive advantage.
Don’t just keep up with, or let compliance slow you down. Book a demo and an intro call today and take the next step towards cloud excellence by automating compliance.