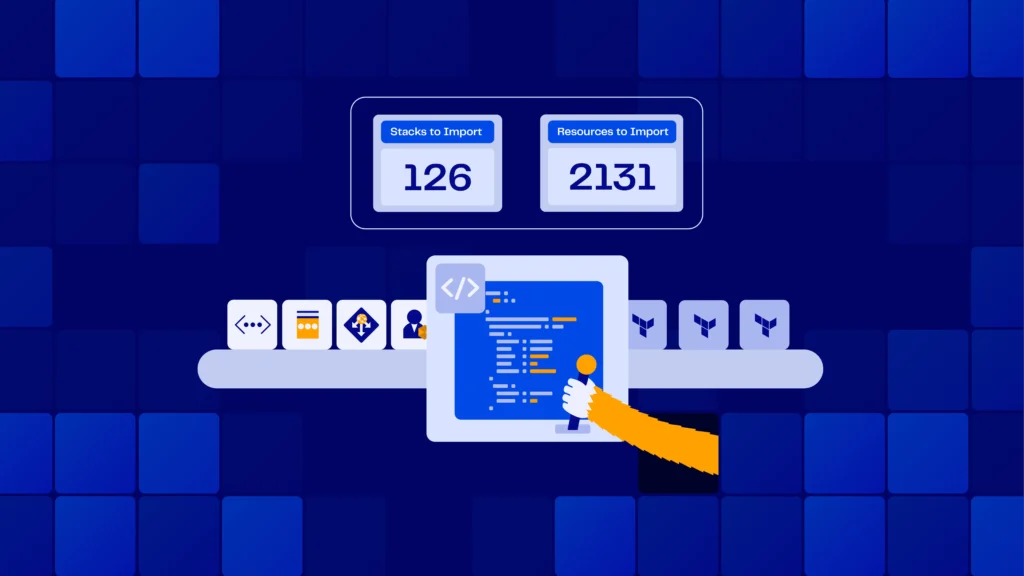
When your delivery pipeline relies on Google Kubernetes Engine, GCP Terraform authentication is the key link that keeps your Git commits secure and your production stable. Automating identity and certificate handling with cloud governance tools removes copy-pasted secrets, eliminates role sprawl, and keeps every Terraform apply reproducible. For a quick start, see how the ControlMonkey GCP Terraform Import Engine finds unmanaged resources. It turns them into code and shows cloud cost-saving opportunities. No manual state changes are needed.
If you are looking for a getting started guide on GCP and Terraform – learn more here
Why GCP Terraform Authentication Matters for Security
Human user accounts may seem convenient, yet they often come with browser cookies, forgotten passwords, and unclear audit trails. Terraform runs belong to machines, so treat them that way. Purpose-built service accounts deliver:
- Narrow, least-privilege IAM roles
- Rotatable machine credentials
- Cloud Audit Logs tied to a single workload
The result is a stronger gcp terraform authentication and gcp terraform security posture that also supports ongoing cloud cost optimization without compromising delivery speed. Need a broader policy view? Check out ControlMonkey’s guide to Terraform cloud governance best practices.
More about GCP and Terraform
-
GCP Cloud SQL Terraform →
Quick Start Guide
-
OpenTofu Multi-Cloud: →
3 IaC Challenges It Solves Across AWS, Azure & GCP
-
Stay in Control: Detect Console Operations on GCP →
Discover your GCP Resource Coverage
Authenticating Terraform with a Service Account
Creating and Scoping the Identity
gcloud iam service-accounts create tf-gke-deployer \
--description="Terraform GKE deployer"
gcloud projects add-iam-policy-binding $PROJECT \
--member="serviceAccount:tf-gke-deployer@$PROJECT.iam.gserviceaccount.com" \
--role="roles/container.admin"The least-privilege model mirrors the AWS IAM best-practice principle of “grant only what’s required.”
Passing Service Account Credentials to Terraform on GCP
gcloud iam service-accounts keys create tf-gke.json \
--iam-account=tf-gke-deployer@$PROJECT.iam.gserviceaccount.com
export GOOGLE_CREDENTIALS="$(cat tf-gke.json)"
provider "google" {
credentials = file("tf-gke.json")
project = var.project
region = var.region
}This Terraform authentication on GCP flow keeps long-lived keys out of repos, rotates them on your schedule, and aligns with broader cloud governance best practices.
Generating PEM-Encoded Cluster Certificates
- When Terraform provisions GKE, it stores the cluster’s CA root in cluster_ca_certificatea base64 PEM string.
- Downstream modules that expect a Terraform GCP cluster certificate PEM-encoded value can consume the output directly—no extra fetch is required, which streamlines pipelines and reduces costs.
- Guard the PEM + valid token carefully: in tandem with a token, it grants API-server access.
Common Misconfigurations in Terraform GCP Authentication
Even with solid gcp terraform authentication in place, four slip-ups surface again and again:
1. Hard-coded service-account keys.
Burying JSON keys in repos or CI variables that never rotate hands attackers a permanent backdoor and undermines your terraform gcp authentication strategy.
Follow Google’s guidance to rotate keys at least every 90 days and prefer short-lived tokens whenever possible. For step-by-step remediation, which walks through vaulting and automatic key rotation.
2. Over-broad IAM scopes.
Granting the roles/owner hammer where a tiny wrench would suffice violates least-privilege principles, inflates spending, and magnifies the blast radius.
Google’s IAM docs recommend assigning the narrowest predefined or custom roles required for a task, Terraform’s google_project_iam_member resource makes right-sizing trivial—use it.
3. Expired or mismatched PEM certificates.
A stale cluster_ca_certificate leads to x509: certificate signed by unknown authority errors that brick kubectl and Helm. Whenever you rotate GKE control-plane certs or recreate a cluster, refresh the PEM in state (or output) so downstream modules stay in sync.
4. Local developer credentials sneaking into CI.
Builds that rely on a laptop’s gcloud config break the moment that machine is offline and leave zero audit trail. Always export GOOGLE_CREDENTIALS from a vetted service account in the runner, and consider enforcing terraform validate checks that block plans using user tokens.
Secure GCP Terraform Authentication Best Practices
By codifying gcp terraform authentication from tightly scoped service accounts to refreshed PEM certificates, you transform identity management from an anxious manual chore into a repeatable, auditable control. The payoff is crystal-clear change history, faster incident response, and a security posture that scales with every new GKE cluster.
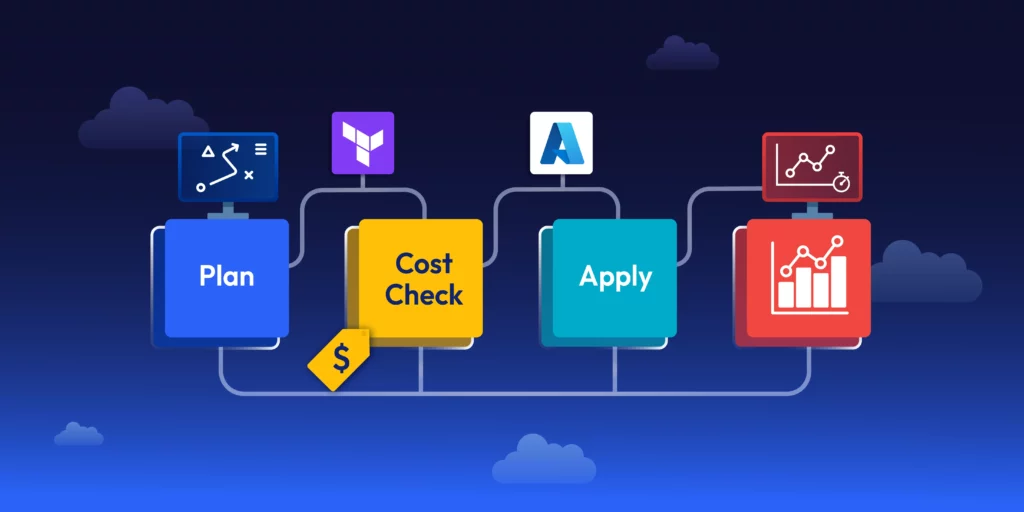
Ready to apply these patterns across your estate? See how ControlMonkey automates drift detection, policy enforcement, and key rotation in one unified workflow book a ControlMonkey demo today.