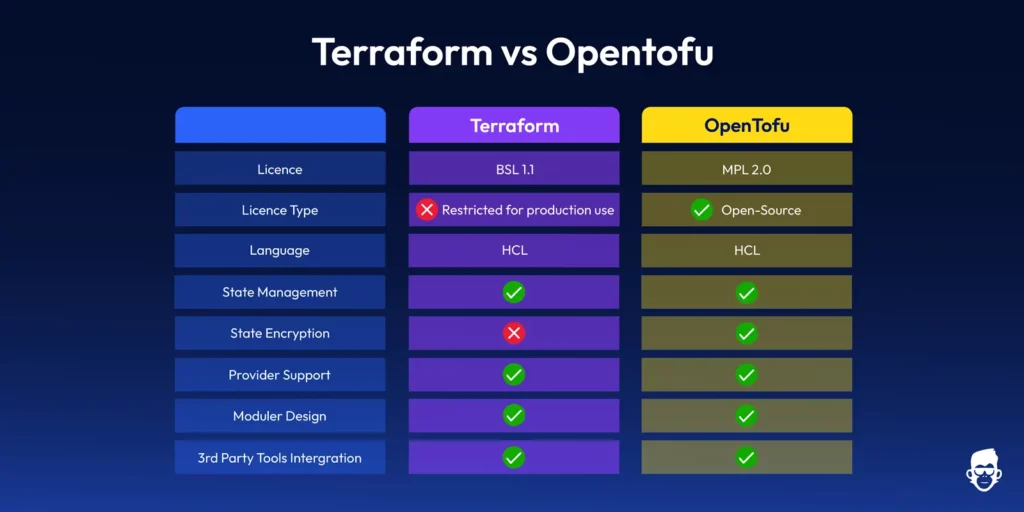
In late 2023, HashiCorp transitioned Terraform away from its established terraform opensource model to a business‑source license, causing uncertainty for many developers. In response, the community created OpenTofu, a fork of the last open-source version of Terraform, and placed it under the Linux Foundation for neutral governance
The community responded by forking the last terraform opensource version, re-branding it OpenTofu, and placing it under the Linux Foundation for neutral governance.
Currently, OpenTofu has matured into a production‑grade tool with a thriving ecosystem that proves the strength of the terraform opensource heritage boasting 4 000+ providers and 20 000+ modules installable from a public registry.
If you’re getting started opentofu with infrastructure as code (IaC) for the first time in 2025, OpenTofu should be your first choice. In fact, OpenTofu offers three big advantages:
- True OSS license – zero friction for side projects, client work, or commercial SaaS.
- Drop-in Terraform compatibility – HCL syntax, and providers still work with no compatibility issues.
- Community-driven roadmap – bug fixes and features land quickly without commercial blockers.
Simply put, OpenTofu gives beginners the power of terraform opensource tooling without worrying about licensing.
🟨 Learn What OpenTofu Is:
Not sure what OpenTofu is or how it fits into your infrastructure workflow. Here are more guides to learn:
- OpenTofu Modules Best Practices: Reuse patterns and IaC blueprints.
- Migrate from Terraform to OpenTofu: 1-click migration with full state conversion.
- OpenTofu vs Terraform: Compare features, licensing, and workflows.
Key OpenTofu Concepts for IaC Beginners
But, before getting started opentofu in a production workflow, it’s important to understand some essentials about the tool:
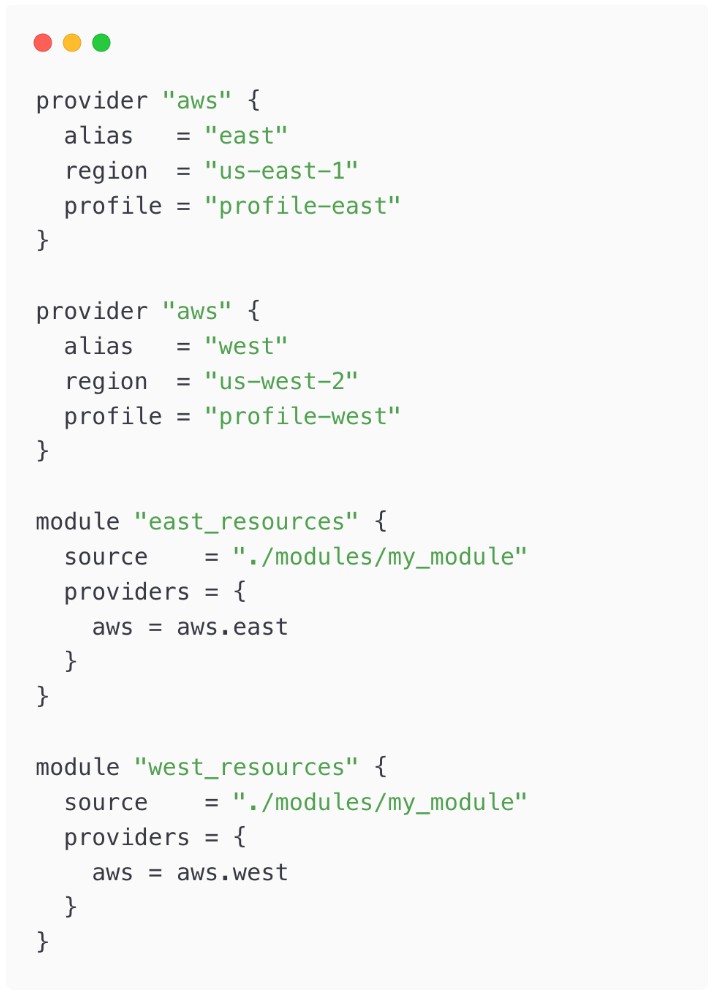
Providers
In OpenTofu, Providers are plugins that just as in the original terraform open-source project let the tool interact with cloud platforms like AWS or Azure. Think of them as a bridge that lets OpenTofu manage cloud resources effectively.
Essentially, when you define an OpenTofu configuration block, it communicates with the cloud provider using the provider APIs and provisions the resource for you.
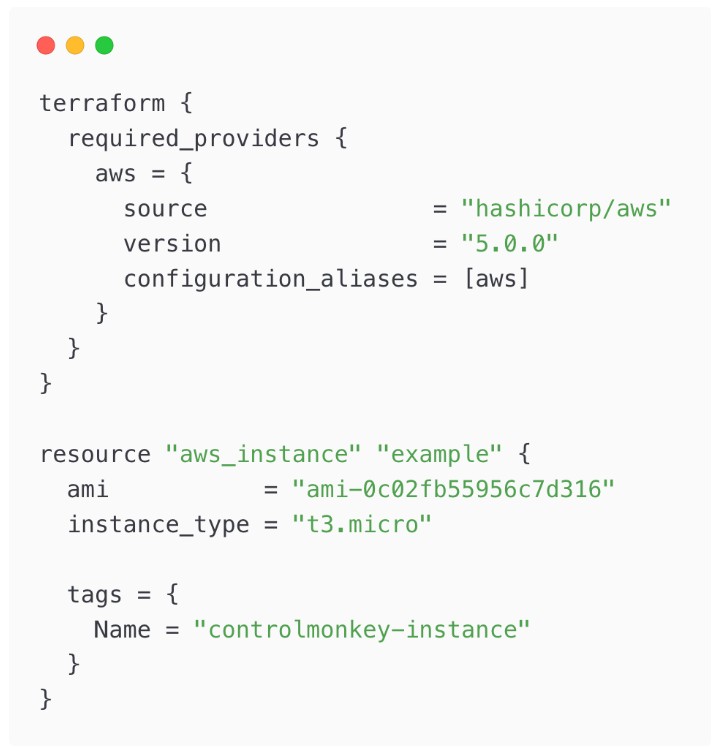
For example, here’s what a provider which communicates to AWS would look like:
terraform {
required_providers {
aws = {
source = "hashicorp/aws" # OpenTofu registry mirrors Terraform namespace
version = "~> 5.29"
}
}
}
provider "aws" {
region = "us‑east‑1"
}The terraform block pins provider versions, while the provider block defines credentials and default regions information OpenTofu needs to plan and provision resources.
Resources
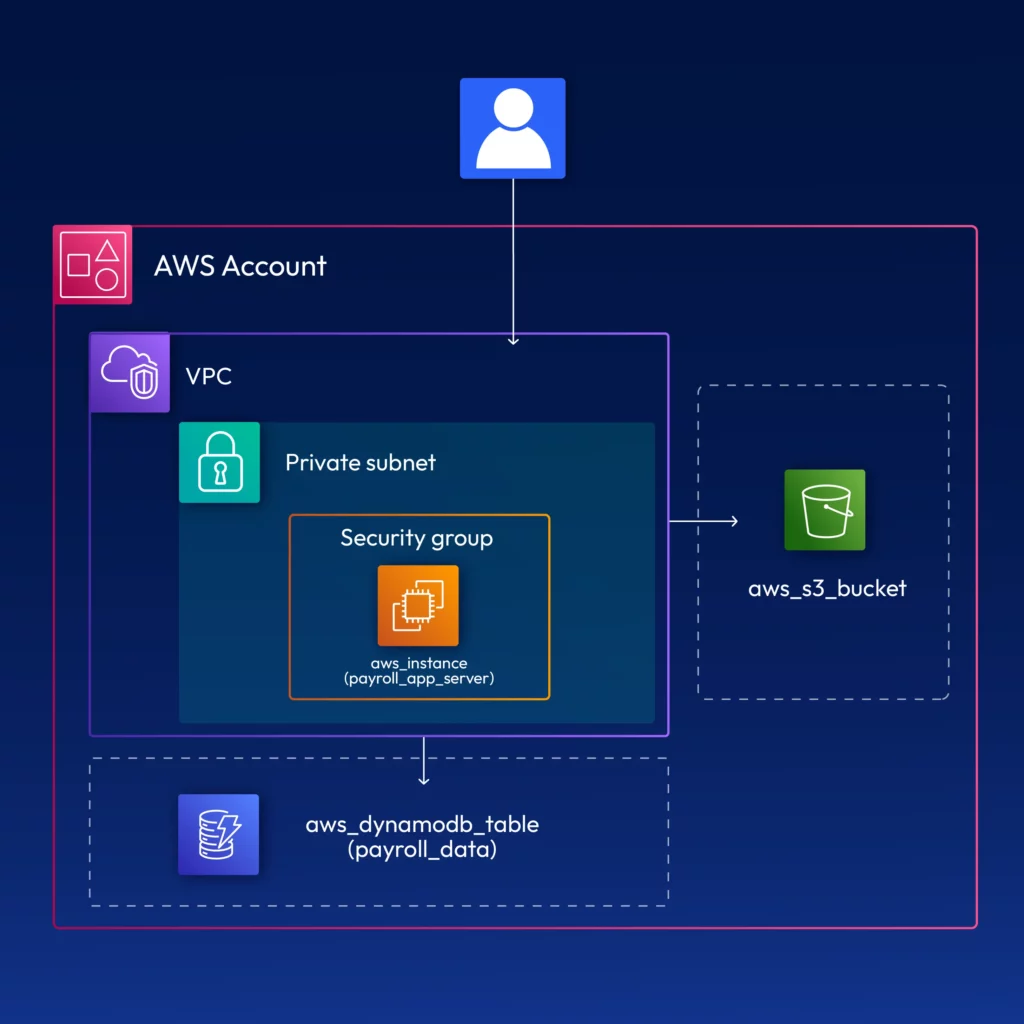
A resource is a declarative block that describes what you want. This could be an S3 bucket, EC2 instance, or VPC, anything cloud-related.
For example, you’d define a resource using the following convention:
resource "aws_s3_bucket" "demo" {
bucket = "otf-demo-bucket"
acl = "private"
}Configuration
Your configuration is defined using .tf files. If you’re familiar with Terraform, you’d have used .tf files. They essentially provide a space which you can use to define cloud infrastructure.
State
In OpenTofu, state is a file that tracks the resources you’ve provisioned in the cloud. It functions like an inventory list that helps OpenTofu detect changes and apply only the necessary updates to your cloud environment.
For instance, if OpenTofu state determines that new resources are present in your configuration which aren’t available in the cloud, it will automatically provision them for you.
This enables drift detection and safe incremental changes.
You can configure your state by defining the state definition in your terraform block:
terraform {
backend "s3" {
bucket = "otf-state-bucket"
key = "global/s3/terraform.tfstate"
region = "us-east-1"
dynamodb_table = "otf-locks" # prevents concurrent applies
encrypt = true
}
}OpenTofu Registry
OpenTofu has a public registry (search.opentofu.org) which provides a catalogue of community-tested providers and reusable modules. You can search, pin exact versions, and even run tofu providers lock to generate dependency hashes for supply-chain security.
Step-by-Step Overview – How does OpenTofu fit into your infrastructure workflow?
If you’re getting started opentofu and working with IaC, you’ll follow a lifecycle as follows:
1. Write Configuration
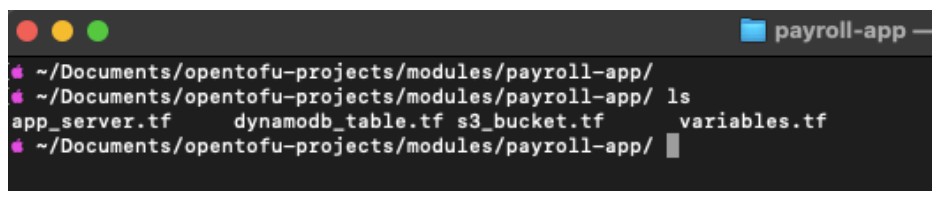
Start by writing a configuration file, typically named main.tf. This file should define the resources you want, such as an S3 bucket, and specify their settings. Example below:
For example, you can define your provider and your resource using the following:
# main.tf
terraform {
required_providers {
aws = {
source = "hashicorp/aws"
version = "~> 5.29"
}
}
}
provider "aws" {
region = "us‑east‑1"
}
resource "aws_s3_bucket" "demo" {
bucket = "otf-demo-bucket"
acl = "private"
}You can define your resources in a main.tf and commit it to a version control system.
2. OpenTofu Initialize
Next, initialize the providers you’ve configured in your terraform block by running tofu init. This prepares the environment for provisioning resources.
This can be done using tofu init. This will:
- Download the AWS provider
- Read your backend settings
- Prepare a working directory.
3. OpenTofu Plan
After you’ve initialized your backend, you can begin a deployment by first gaining an insight on what’s going to be applied on your IaC configs. This can be done by executing the command:
tofu plan
By doing so, it will generate a difference on what will be created, removed and modified in the cloud.
In your case, you’ll see resources being generated as you’ll be provisioning for the first time.
4. OpenTofu Apply
After you have reviewed the plan, you can run tofu apply. This will apply the changes on your cloud environment and will provision the defined IaC in the cloud.
5. Safely Update IaC with OpenTofu
Later you can add versioning or encryption. plan shows a minor in-place update, and apply executes it without touching other resources.
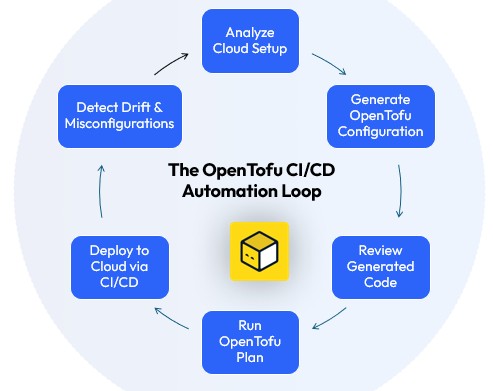
6. Introduce CI/CD
Once you’re comfortable with the manual deployment process, you can enhance your workflow by automating it through a CI/CD pipeline. This approach is particularly useful for teams working on large-scale projects.
You can configure your pipeline rules in a way that every pull request triggers a plan and only merges to main trigger an apply. A sample GitHub Actions pipeline that many teams adopt when getting started opentofu looks like this:
name: OpenTofu CI
on:
pull_request:
paths: ["**.tf"]
jobs:
plan:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Set up OpenTofu
uses: opentofu/setup-opentofu@v1
- name: Cache providers
uses: actions/cache@v4
with:
path: ~/.opentofu.d/plugins
key: ${{ runner.os }}-tofu-${{ hashFiles('**/.terraform.lock.hcl') }}
- name: Init
run: tofu init -input=false
- name: Plan
run: tofu plan -input=false -no-color | tee plan.txt
apply:
needs: plan
if: github.ref == 'refs/heads/main' && github.event_name == 'push'
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- uses: opentofu/setup-opentofu@v1
- name: Init
run: tofu init -input=false
- name: Apply
env:
TOFU_CONFIRM: "true"
run: tofu apply -input=false -auto-approve
This workflow gives you automated drift detection on every PR and a tamper‑proof audit trail in GitHub.This workflow gives you automated drift detection on every PR and a tamper‑proof audit trail in GitHub.
Scaling OpenTofu for Teams and Environments
Once you’re getting started opentofu and comfortable with the basics, you can explore advanced workflows, such as:
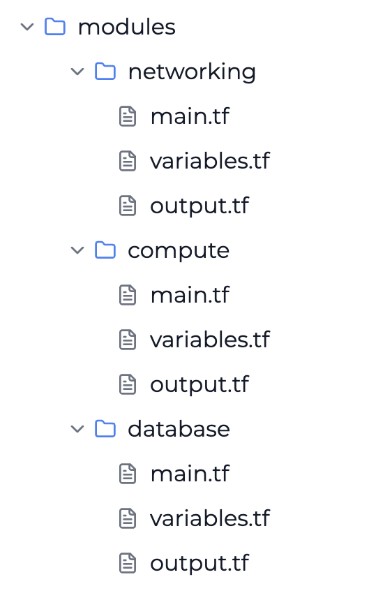
1. Reuse patterns
Use OpenTofu Modules. Publish a VPC or EKS blueprint to your private registry so every micro-service team can consume it with a single block.
2. Automate plans/applies
Use CI/CD runners (e.g., GitHub Actions, GitLab, Jenkins) to call OpenTofu in plan-only mode and require a human-approved pull-request label before the apply job runs.
3. Manage multiple environments
Adopt a separate state backend per account/region pair. Tools like OpenTofu’s native -chdir= flag simplify mono-repo layouts.
3. Migrate existing Terraform code
You often just rename the binary to tofu, update provider constraints if necessary, and run tofu init.
However, you can use a more safer and guided migration approach by using ControlMonkey. It offers a 1-click migration wizard that converts your state and CI pipelines automatically onto an OpenTofu workflow.
📘🟨 More on Scaling OpenTofu
- Troubleshooting OpenTofu Errors : Common issues and how to fix them at scale.
- Multi-Cloud with OpenTofu : Manage AWS, Azure, and GCP with unified IaC
🟨 OpenTofu: Concluding thoughts
Picking an IaC framework used to be a trade-off: Open-source freedom vs. corporate support.
OpenTofu closes that gap.
It keeps Terraform’s proven workflow, removes license uncertainty, and adds a faster-moving community roadmap.
If you already have Terraform code and want to see OpenTofu in action, ControlMonkey’s 1-click migration spins up a free sandbox, converts your state, and rolls back in seconds if you change your mind. Ready to migrate from Terraform to OpenTofu? Book a demo with ControlMonkey and see how simple it can be.