Modern companies depend on Cisco Meraki to keep offices, branches, retail locations, and distributed teams connected. From employee Wi-Fi and guest access to firewall rules, VLAN segmentation, site-to-site VPNs, and traffic shaping policies, Meraki controls the network configuration layer that keeps people, devices, and business-critical applications online.
But while cloud infrastructure and application data are often covered by disaster recovery plans, office and branch network configurations are still frequently changed manually, undocumented, or left outside formal recovery strategies. One deleted firewall rule, broken VLAN, misconfigured VPN, or incorrect traffic policy can disrupt employee access, disconnect locations, or impact critical operations.
ControlMonkey now supports Cisco Meraki Backup, helping teams automatically back up, track, and recover critical Meraki configurations before network changes become business disruptions.
Introducing Cisco Meraki Backup and Recovery
With ControlMonkey, teams can protect key Cisco Meraki configurations, including:
- Firewall filtering rules that control access and network security
- VLAN configurations that define internal network segmentation
- Site-to-site VPN settings that connect offices, branches, and distributed environments
- Traffic shaping policies that manage bandwidth and application performance
- Network configuration changes that need visibility, versioning, and fast recovery
Why Do You Need a Resilience Solution for Cisco Meraki?
Cisco Meraki controls critical office and branch connectivity. If firewall rules, VLANs, site-to-site VPN settings, or traffic shaping policies are changed or deleted, the impact can be immediate: users lose access, offices go offline, security policies break, and IT teams are forced to troubleshoot under pressure.
There are few risk vectors:
- It could be an honest mistake of one of your employees
- Malicious actor trying to shut down your office
- or an over-permissive AI agent that made a change it shouldn’t.
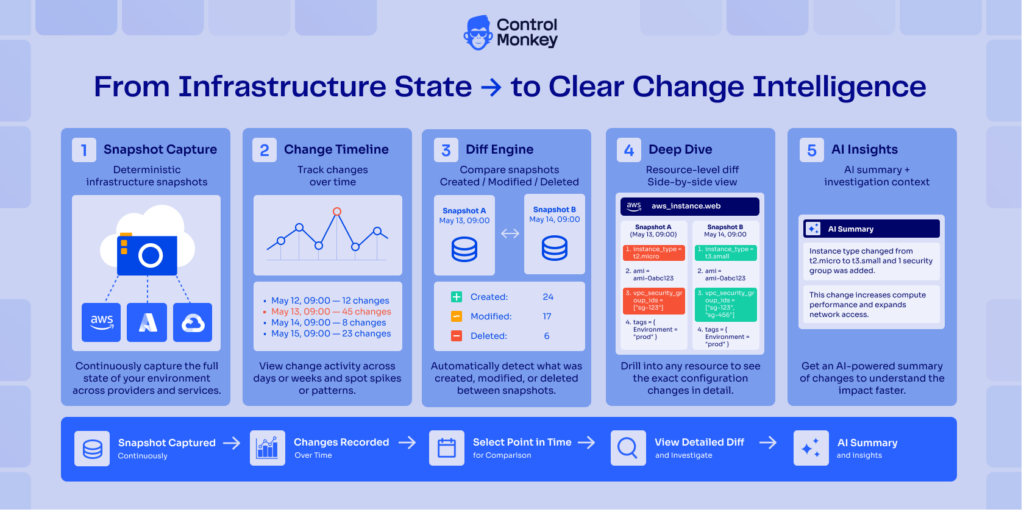
ControlMonkey gives teams a reliable recovery path for Cisco Meraki configuration. Instead of relying on manual investigation or tribal knowledge, teams can track configuration changes over time, identify creations, modifications, and deletions, and restore a previous known-good state when needed.

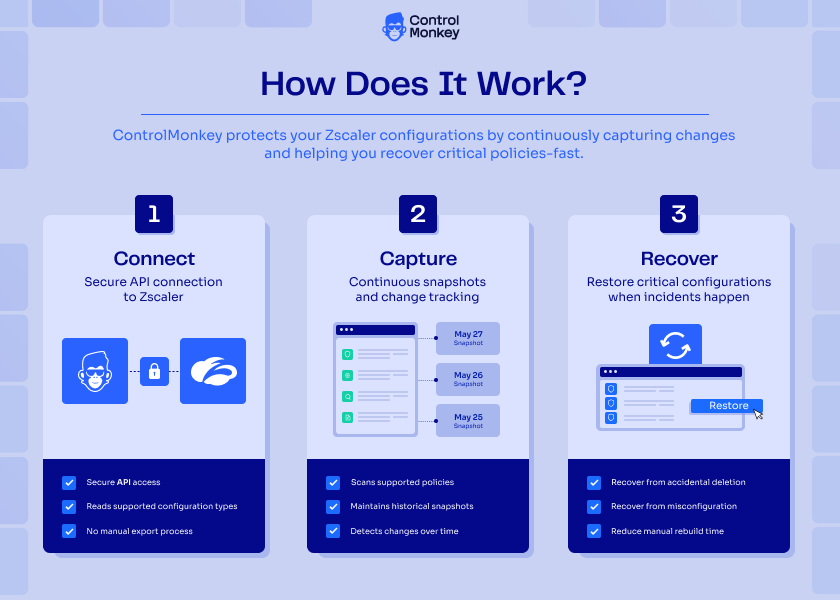
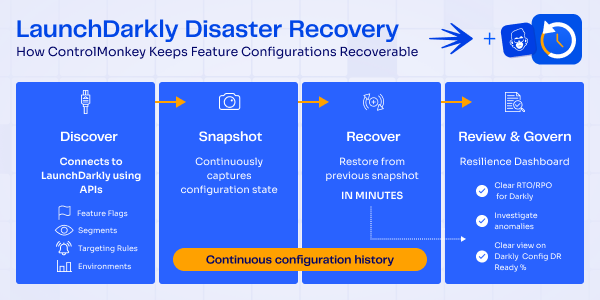
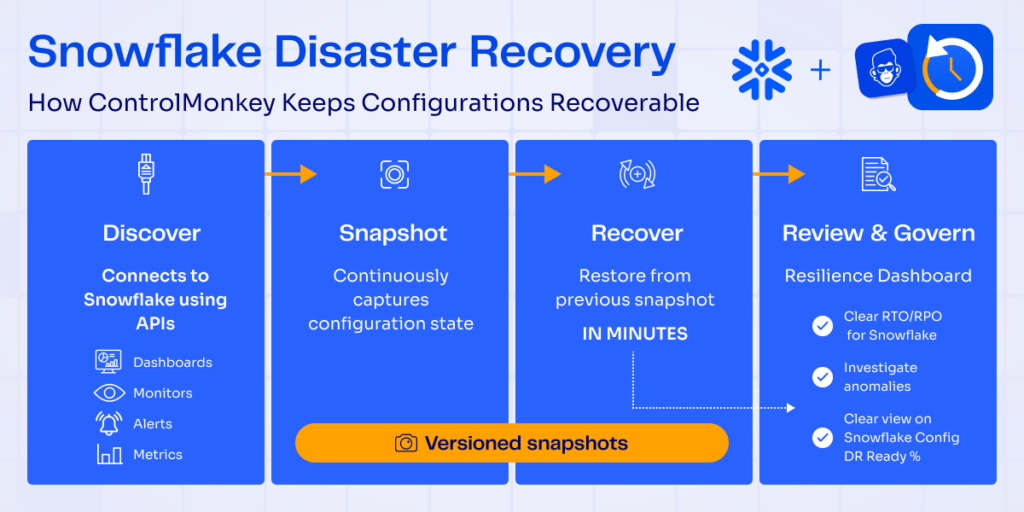
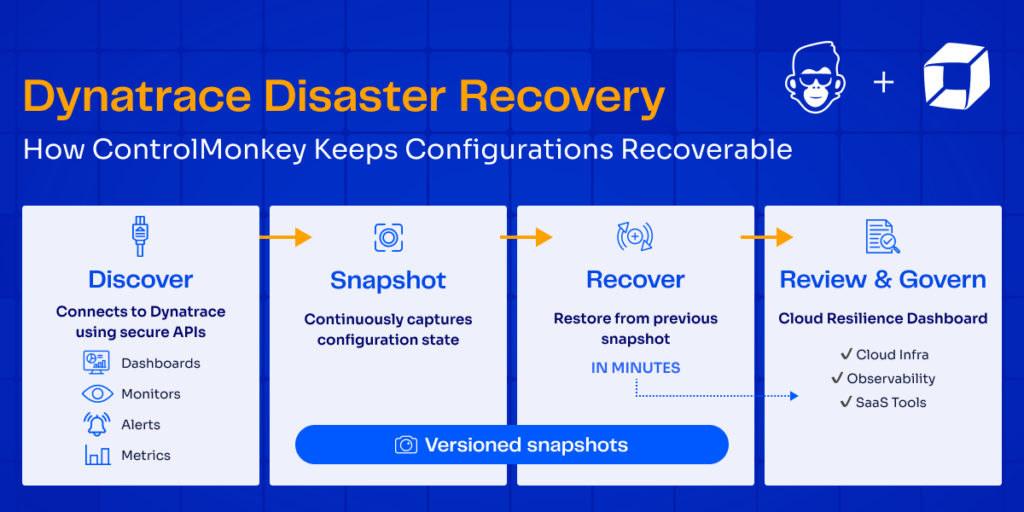
How Does Cisco Meraki Disaster Recovery Work?
ControlMonkey connects to your Cisco Meraki environment and continuously scans supported network configurations, including firewall filtering rules, VLANs, site-to-site VPN settings, and traffic shaping policies.
Each configuration state is automatically backed up and versioned, so teams can track changes over time and identify what changed, when it changed, and what needs to be restored.
If a configuration is deleted, misconfigured, or changed unintentionally, ControlMonkey enables teams to recover the previous state quickly – reducing downtime risk and protecting office and branch connectivity.
You can also use the daily snapshot to replicate your Meraki configuration to a new tenant or office. This makes it easy to copy your configurations in the event of a ransomware attack or when you need to quickly spin up a new site.

How ControlMonkey Is Different
Traditional Cisco Meraki backup vendors help teams protect Meraki configurations such as firewall rules, VLANs, site-to-site VPNs, and traffic shaping policies. ControlMonkey goes further by making Meraki part of a broader cloud and SaaS configuration disaster recovery strategy.
That means Cisco Meraki is protected alongside the other configuration layers that keep the business running : cloud resources, DNS, CDN, identity, observability, databases, version control systems, and third-party SaaS platforms.
Instead of treating Meraki as a standalone network backup workflow, ControlMonkey helps teams answer a bigger resilience question: Can we restore how our environment was configured not just recover our data?
ControlMonkey vs. Traditional Cisco Meraki Backup Vendors
| ControlMonkey | Traditional Vendor | |
|---|---|---|
| Focus | Disaster recovery for cloud, SaaS, network, identity, and infrastructure configuration | Meraki or network configuration backup and rollback |
| How Meraki Is Treated | Protects Meraki as part of the broader business configuration layer | Protects Meraki mainly as a standalone network platform |
| Configuration Scope | Covers Meraki as part of a wider cloud, SaaS, identity, observability, and network configuration DR strategy | Focuses mainly on Meraki/network configuration history and restore |
| Recovery Approach | Uses versioned snapshots so teams can restore Meraki configurations to a previous known-good point in time | Enables rollback or restore of Meraki/network settings |
| Governance Value | Provides visibility into DR readiness, backup coverage, recovery gaps, and resilience posture | Provides network change tracking, backup history, and restore options |
| Operational Outcome | Detects ClickOps and drift, helps teams remediate unintended changes, and keeps configurations aligned with the desired state | Helps network teams recover specific Meraki or device-level configurations after a change or failure |
| Best Fit | Organizations that want unified configuration DR, drift detection, and remediation across cloud, SaaS, identity, network, and infrastructure | Network teams looking for a dedicated Meraki backup solution |
Bottom line: Cisco Meraki backup is not new. What makes ControlMonkey different is that Meraki becomes part of a unified configuration disaster recovery strategy — with point-in-time snapshots, ClickOps visibility, drift detection, and remediation across the configuration layer the business depends on.
Stay Ahead with Cisco Meraki Backup and Recovery!
ControlMonkey extends disaster recovery beyond cloud resources and into the network control plane.
By supporting Cisco Meraki Disaster Recovery, ControlMonkey helps teams improve visibility, reduce operational risk, and recover faster from accidental changes, misconfigurations, unauthorized updates, or automation errors.
Now, Meraki configurations can be protected alongside cloud, SaaS, identity, observability, and infrastructure configurations — giving teams a more complete resilience strategy across the systems that keep the business running.
With ControlMonkey, teams can scale office and branch network operations with more confidence, knowing that critical Meraki configuration is backed up, versioned, and recoverable.
Ready to protect your Cisco Meraki configurations?