PCI-DSS (Payment Card Industry Data Security Standard) is a set of security standards designed to ensure the secure handling of payment card information by organizations. Achieving PCI DSS compliance is crucial for businesses that handle credit card transactions to protect sensitive data and maintain the trust of their customers. While many organizations focus on detective controls to respond to compliance violations, it’s equally important to adopt a proactive approach to prevent violations from occurring in the first place.
PCI-DSS compliance includes infrastructure-related controls that can be validated using a shift-left methodology long before any changes are made to your infrastructure.
In this blog post, we will explore how you can enforce PCI DSS compliance proactively by leveraging Terraform in your infrastructure CI/CD pipeline. We’ll also discuss the benefits of moving away from a reactive approach that relies solely on alerting and investigation. Let’s dive in.
Detective Controls and Their Limitations
Detective controls involve monitoring your environment for violations of PCI-DSS compliance and reacting when such violations occur. This approach typically relies on tools like AWS Security Hub to generate alerts when non-compliance is detected.
While detective controls are essential for identifying and responding to security incidents, they have their limitations:
- Reactive Nature: Detective controls are inherently reactive, meaning you respond to violations after they occur. This can lead to delayed response times and potential penalties.
- Resource-Intensive: Managing alerts, investigations, and remediation can be resource-intensive, requiring a dedicated team and effort.
- Compliance Penalties: Failing to address compliance violations promptly can result in penalties, fines, and damage to your organization’s reputation
The Proactive Approach with Terraform
To take a more proactive stance towards PCI-DSS compliance, consider integrating compliance controls directly into your Terraform CI/CD pipeline. This approach allows you to catch compliance issues before they are introduced into your infrastructure, reducing the reliance on detective controls.
Here’s how you can achieve this:
- Terraform CI/CD Integration: Incorporate PCI-DSS compliance checks into your Terraform CI/CD pipeline. This involves running compliance validation checks during the pull request phase, well before any code is merged and applied to your infrastructure.
- Policy as Code: Implement PCI DSS controls using tools like Open Policy Agent (OPA) or other policy enforcement tools. Define your compliance policies as code and enforce them automatically during the CI/CD process.
- Preventive Measures: By implementing compliance checks early in the development lifecycle, you can prevent non-compliant changes from progressing further, reducing the chances of compliance violations.
PCI-DSS Infrastructure-Related Controls Example
Let’s take a look at two example PCI-DSS controls that are infrastructure-related, on AWS, and can be enforced in the Terraform CI/CD phase:
- Example 1: Encryption of Data at Rest
- Policy: Require that all data stored on persistent disks must be encrypted.
- Terraform Implementation: On any PR check that all data storage resources (e.g., Amazon EBS volumes) are configured with encryption enabled.
- Example2: Encryptions keys should be rotated on a periodically basis
- Policy: Require that all keys are rotated every 90 days.
- Terraform implementation: On any PR ensure that your Amazon KMS Key are configured with ‘enable_key_rotation‘ set to true
ControlMonkey – PCI-DSS Compliance with Terraform Out of the Box
Here at ControlMonkey we always think how we can take the undifferentiated heavy lifting from our customers so they can focus on innovation and less on firefighting compliance issues.
ControlMonkey provides PCI-DSS compliance controls out of the box, with a convenient one-click solution that enables all PCI-DSS infrastructure-related controls and requirements.
We’ve transformed SecurityHub’s PCI-DSS detective controls into proactive controls, eliminating the need for users to write or manage any code. We handle all the complex tasks, making compliance management effortless.
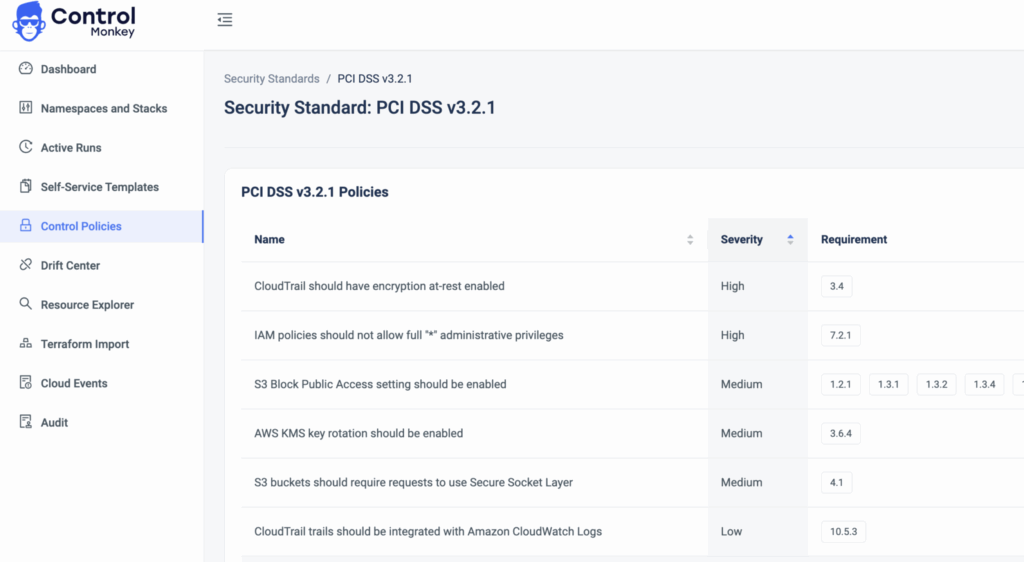
With ControlMonkey, you can enable compliance checks for specific parts of your infrastructure effortlessly and benefit from ‘Always-Compliant’ environments. Here’s how it works:
- Decision on Compliance Scope: Decide which parts of your infrastructure require PCI-DSS compliance.
ControlMonkey allows you to customize the compliance scope to fit your specific needs with our namespaces and stacks hierarchy. - Automated Compliance Checks: ControlMonkey continuously monitors your Terraform codebase for changes and checks that they adhere to PCI-DSS compliance requirements.
- Peace of Mind: With ControlMonkey in place, you can rest assured that any changes made to your Terraform code will be validated for compliance automatically, reducing the risk of non-compliance issues.
Summary
In the world of PCI-DSS compliance, being proactive is key to avoiding penalties and securing sensitive payment card data. By integrating compliance controls into your Terraform CI/CD pipeline or using tools like ControlMonkey Infrastructure CI/CD, you can prevent compliance violations before they occur, reduce the burden of detective controls, and enhance the security of your payment processing infrastructure. Take the proactive approach to PCI-DSS compliance and protect your organization from potential risks.