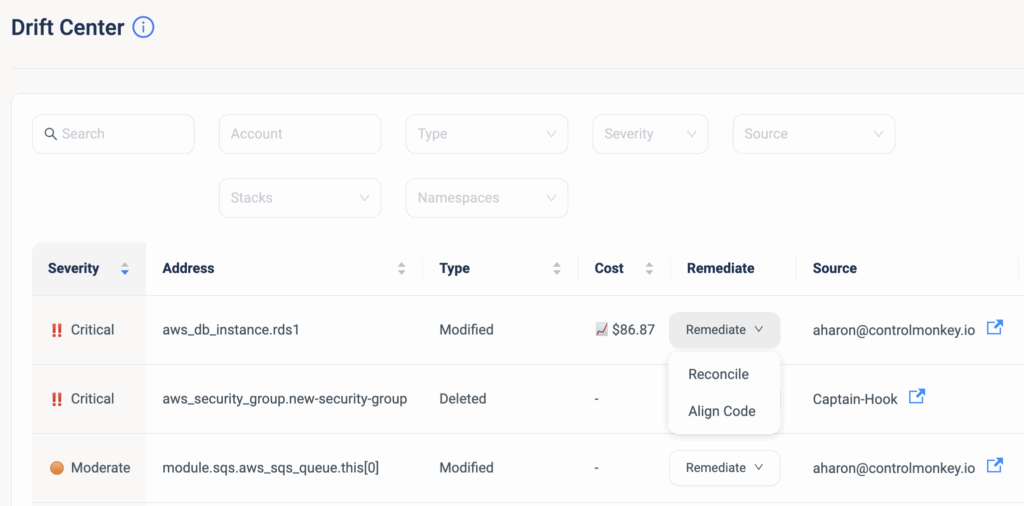
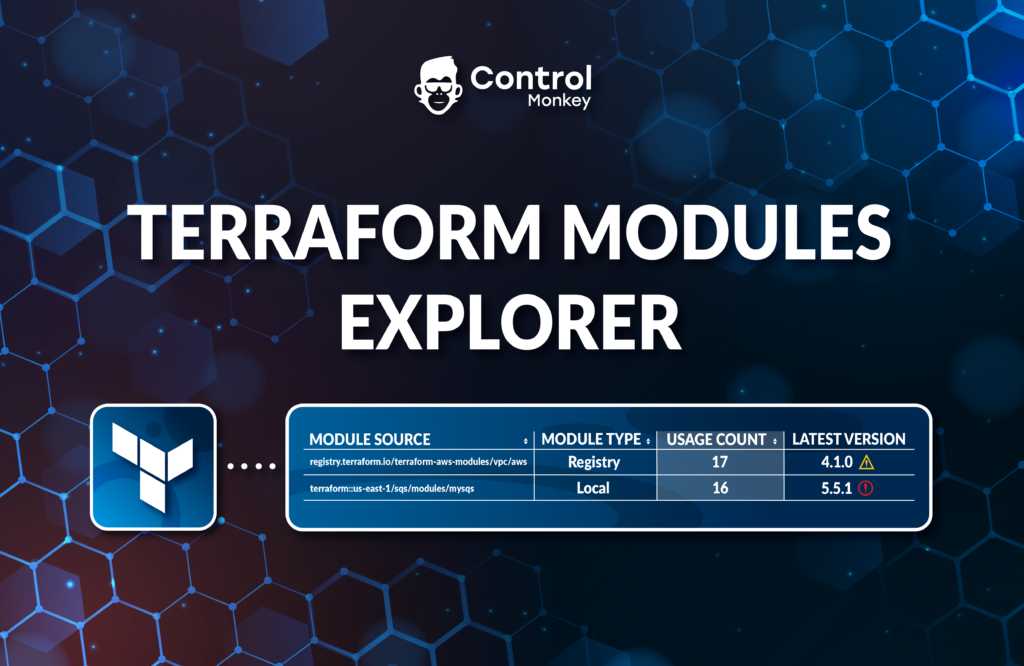
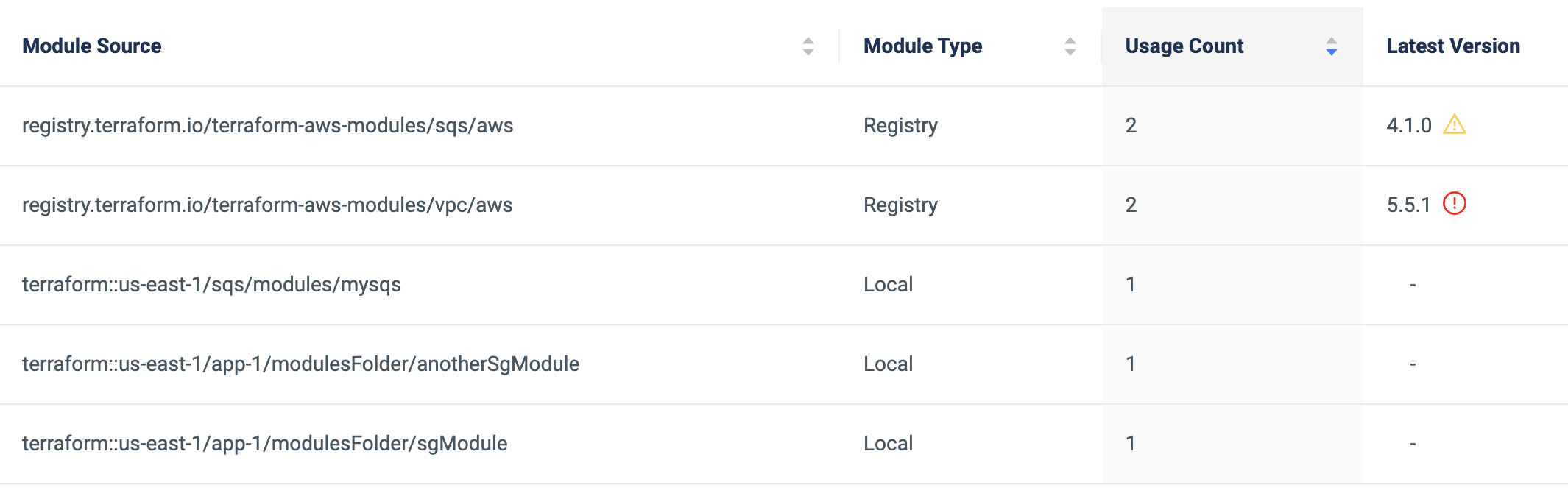
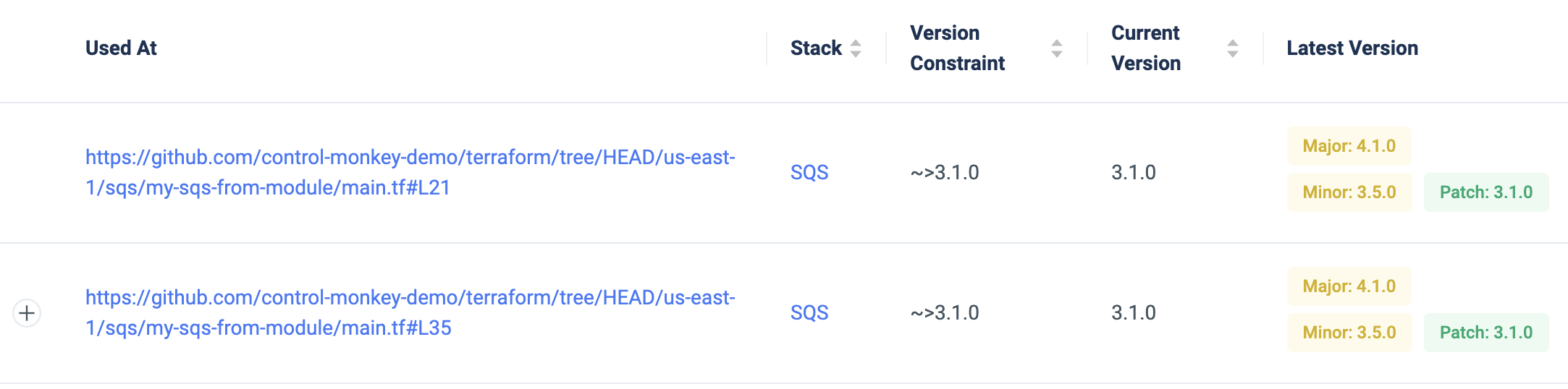
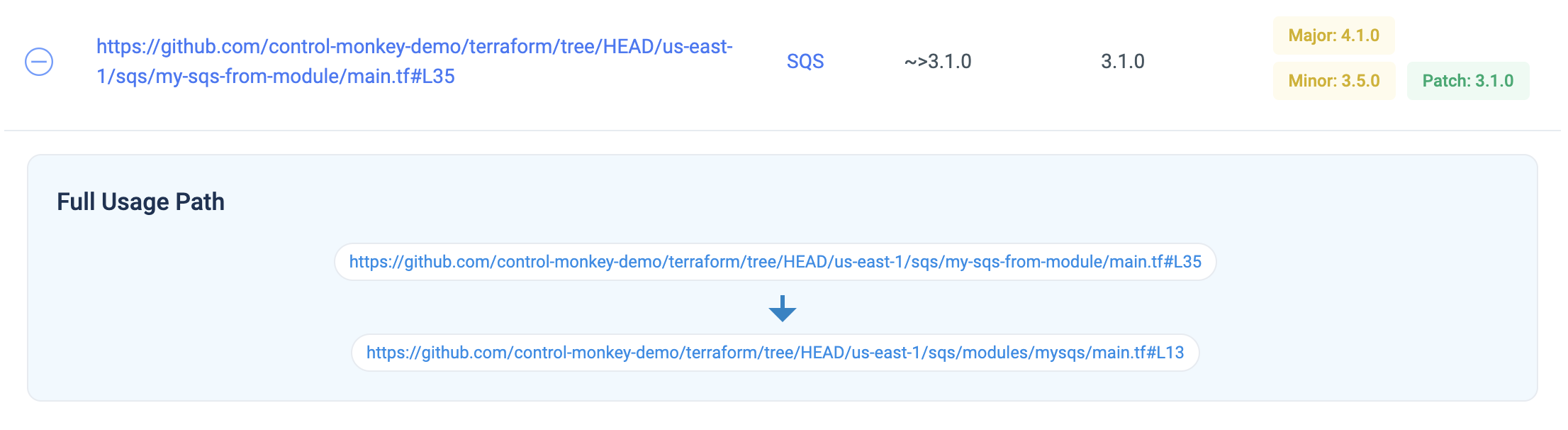
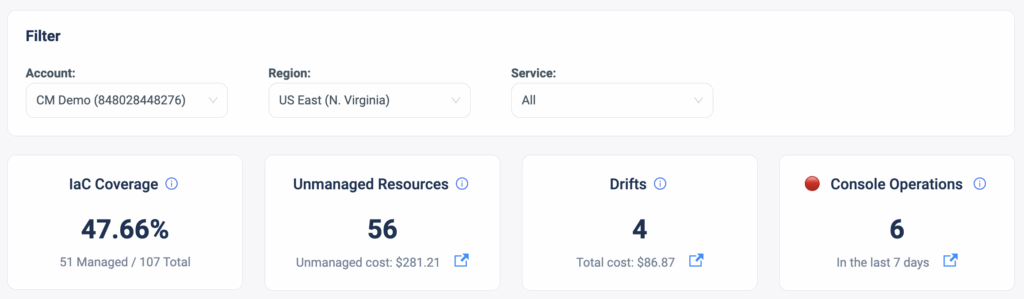
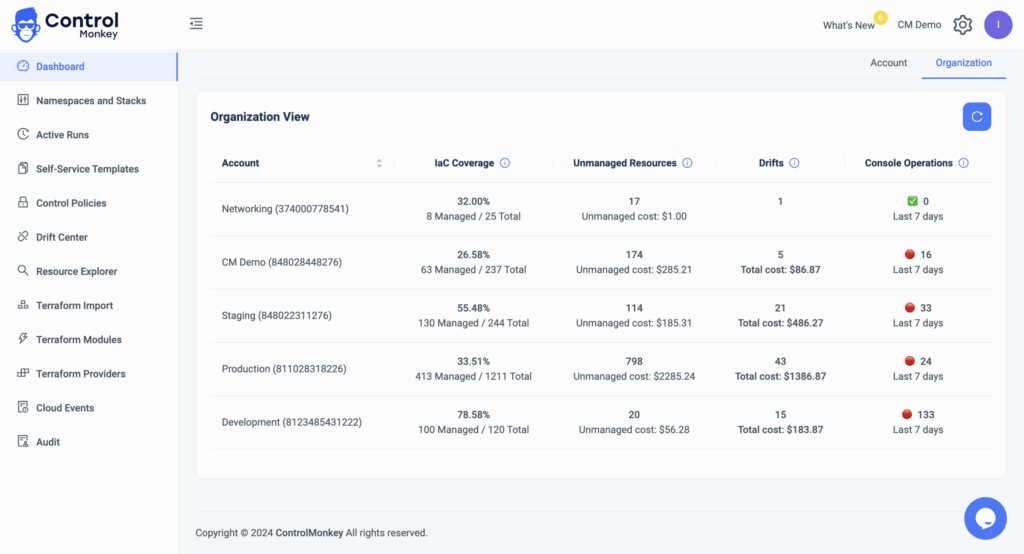
As part of the main dashboard view in the ControlMonkey platform, our users gain visibility into several metrics of interest that provide an overview of the AWS account’s status in terms of IaC coverage, Unmanaged Resources, Terraform Drifts, and Console Operations (ClickOps).
About IaC Posture Dashboard
These metrics help our customers understand the level of control they have over their cloud accounts and point out the gaps that require resolution.
For example, Console Operations are a source for Terraform drifts that can potentially cause misconfigurations.
However, our large customers who hold dozens of AWS accounts requested a holistic view that will help them oversee the bigger picture of their organization. Meaning, that rather than toggling between accounts to get the environments’ status, they wanted to get a 30K feet view of all their accounts in one dashboard.
So today we are pleased to announce the latest enhancement to our Cloud Inventory dashboard, Organization View.
Organization View: IaC Posture Dashboard
The Dashboard Organization View is a Cross-organization visualization of all your AWS accounts, with the option to drill down into any specific account, with a click of a button.
This dashboard provides DevOps with a clear and general view of all their AWS accounts so they can understand the gaps and level of control they have over their cloud.
Do you have dozens of accounts and are interested in learning how ControlMonkey helps you manage them more efficiently?
Our team is waiting to speak with you !