Today we are glad to announce that we have added NIST Compliance to our Proactive Compliance Packages enforcement, as part of the Terraform CI/CD solution.
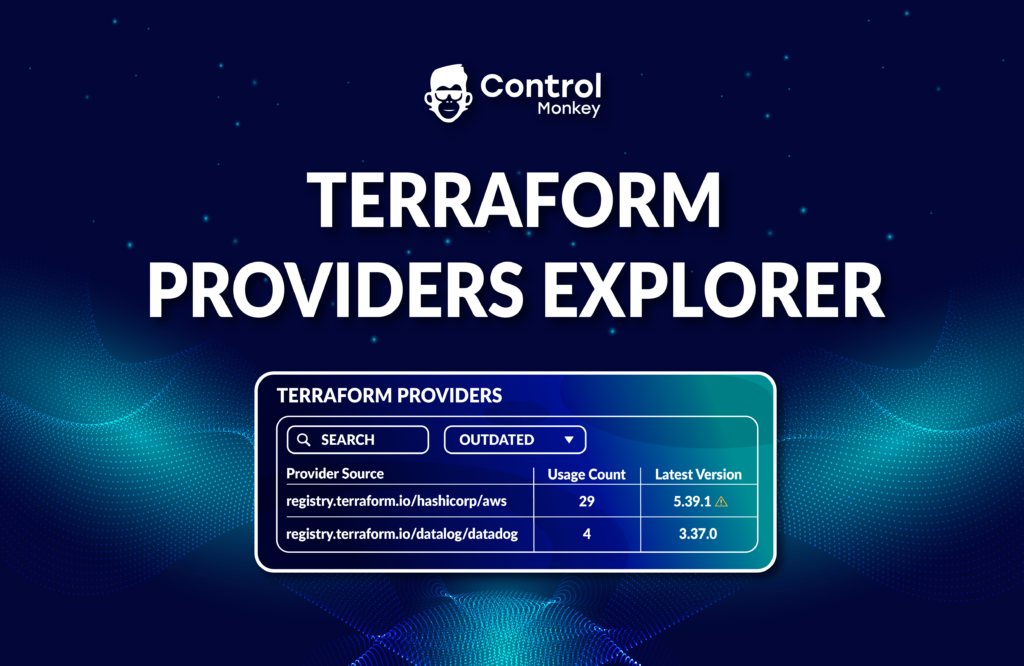
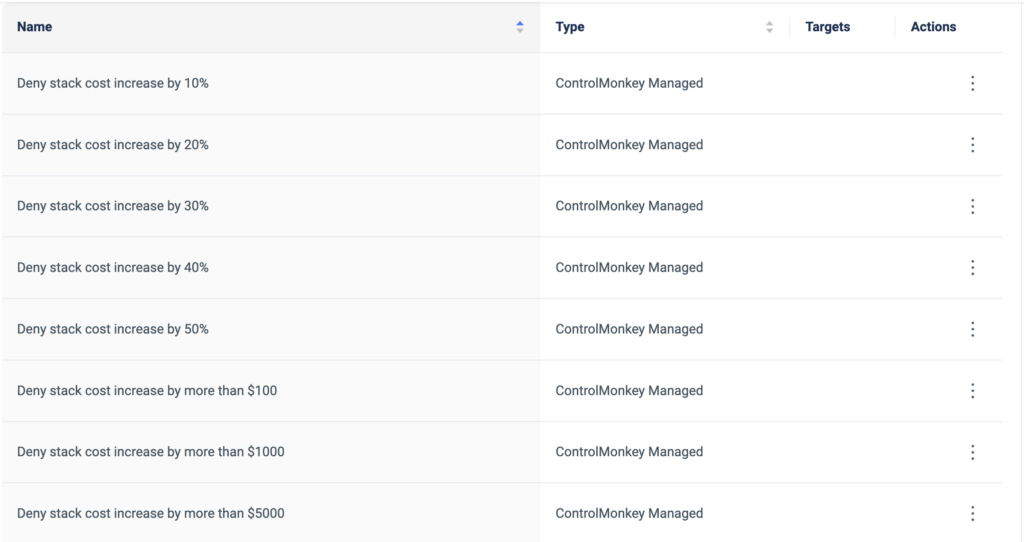
ControlMonkey Terraform CI/CD solution enables DevOps teams to proactively enforce compliance and security policies during the infrastructure CI/CD and prevent issues and misconfigurations in production.
Starting today, our users can enforce NIST 800-53 compliance standards on any Terraform pull request, and ControlMonkey will validate the resources configuration, as part of the infrastructure CI/CD.
Organizations usually run compliance validations in a detective way, after the resources are deployed to production, using tools like AWS Security Hub.
This capability enables DevOps teams to easily enforce NIST Compliance standards proactively, rather than responding to non-compliant resources in production, and risk getting penalized for NIST compliance violations.
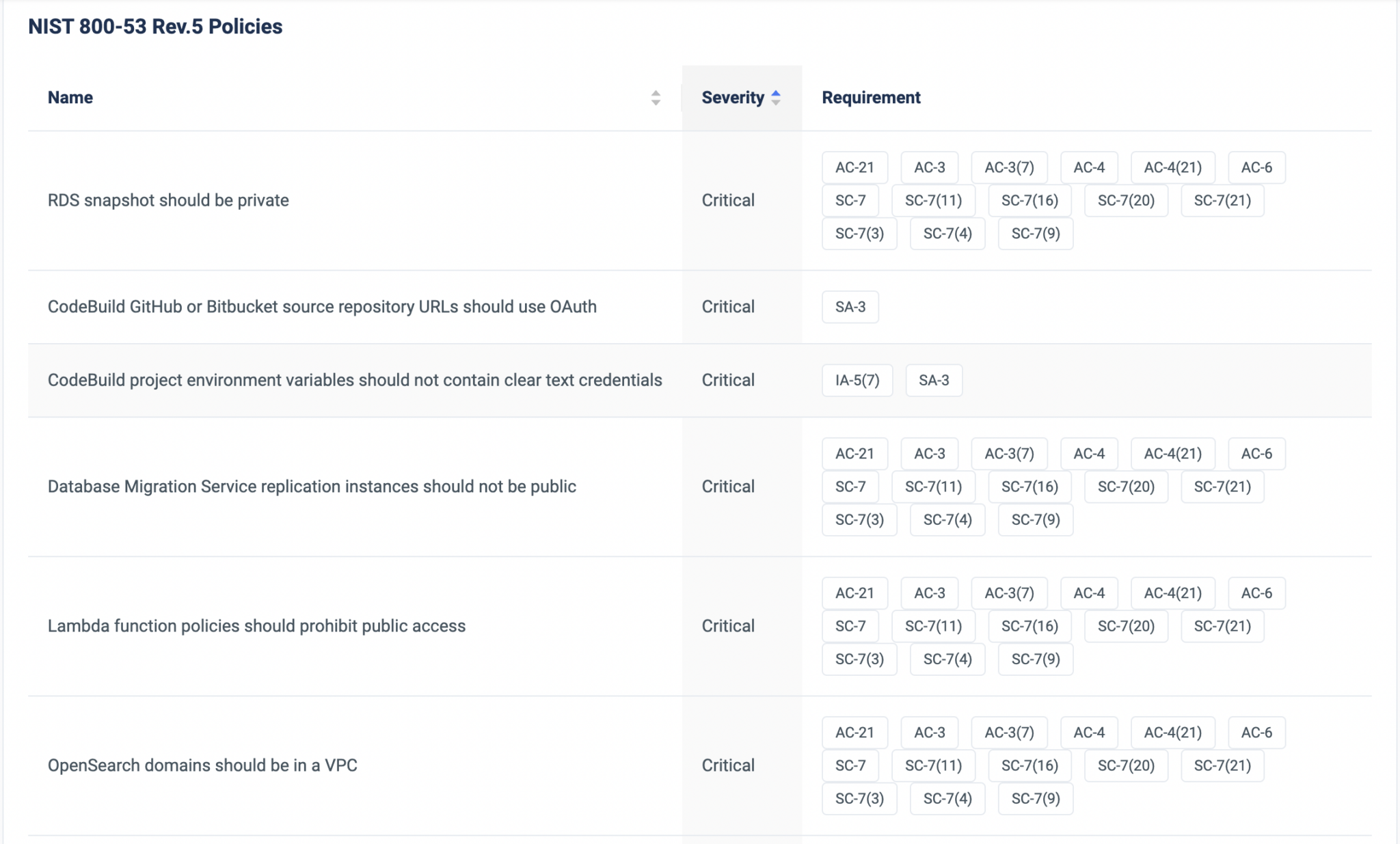
If regulation requires your infrastructure to be NIST compliant, you can validate every resource’s compliance proactively, out of the box, with zero effort.
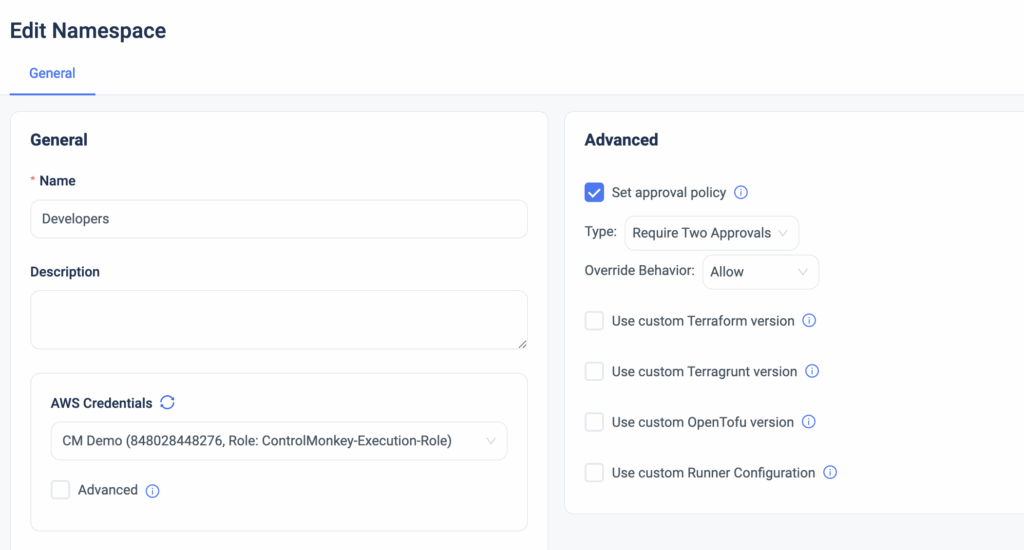
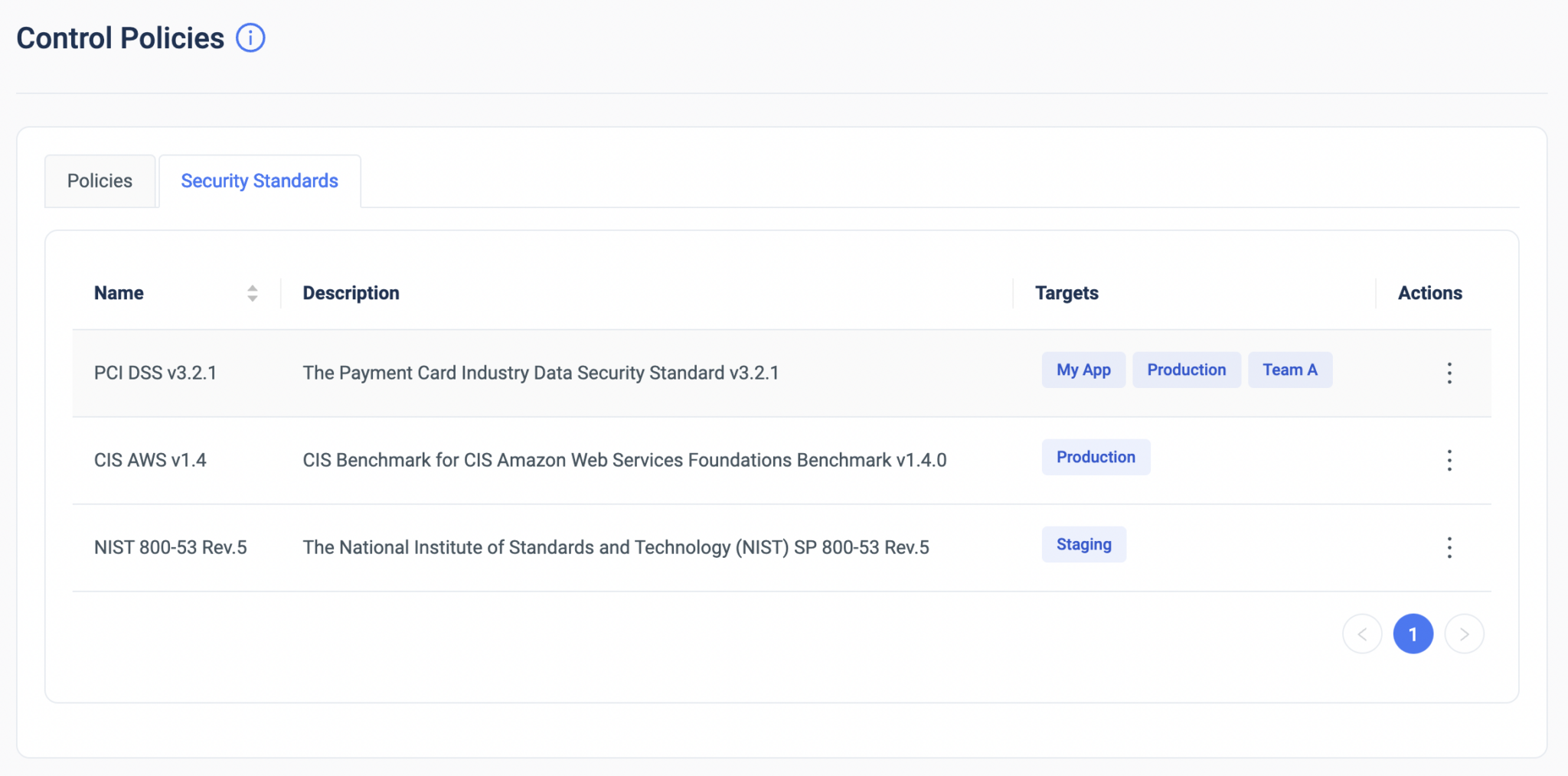
On top of that, users have enhanced customization and granularity and can enforce compliance using various enforcement levels and apply them to specific stacks or namespaces.

Shift left your infrastructure compliance, keep your environment in ‘Always-Compliant’ mode, and allow your team to build faster without sacrificing control.