Cloud governance doesn’t stop at AWS, Azure, or GCP. As monitoring stacks grow more complex, DevOps teams need visibility and control across every layer – including Datadog. That’s why ControlMonkey now offers full support for Datadog Terraform Provider, bringing automation, inventory, and disaster recovery to your Datadog environment through Terraform and OpenTofu.
Introducing Datadog Support in ControlMonkey
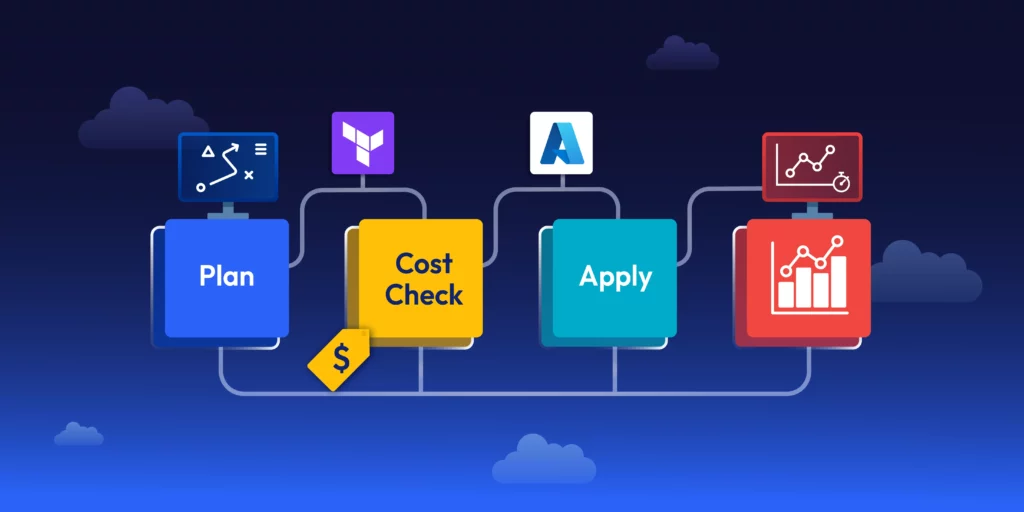
With Datadog support now available, ControlMonkey enables:
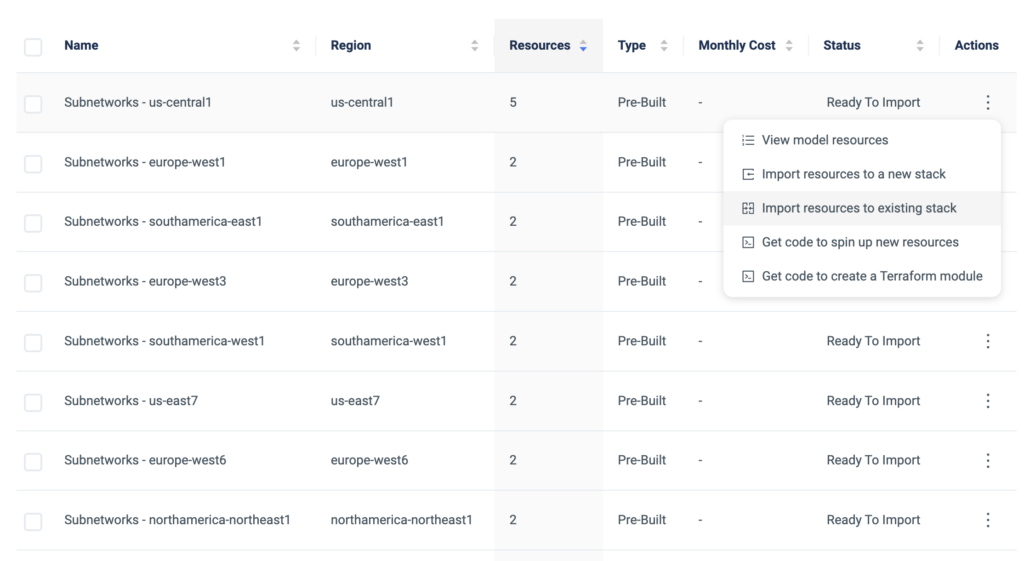
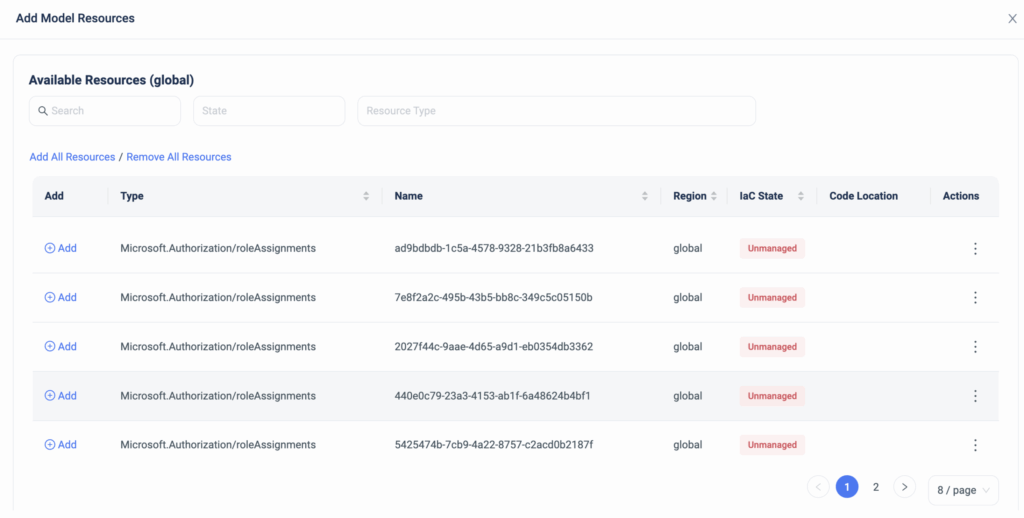
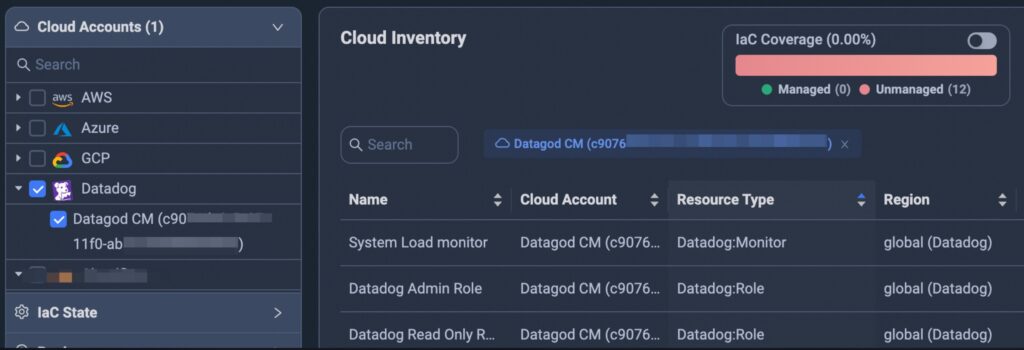
Inventory of Datadog Assets
Unified visibility across dashboards, monitors, alerts, users, and roles.
IaC Coverage Assessment
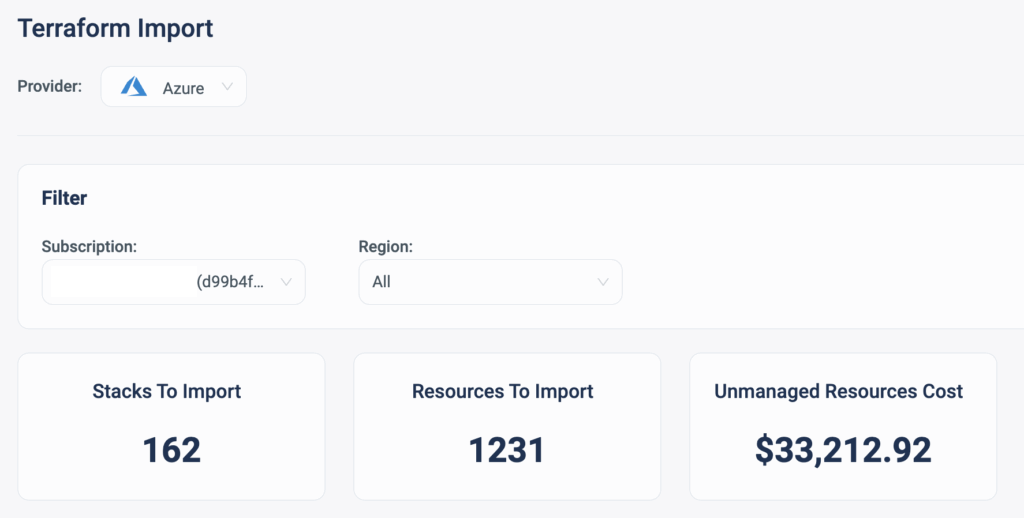
Know instantly which resources are managed by Terraform and OpenTofu –
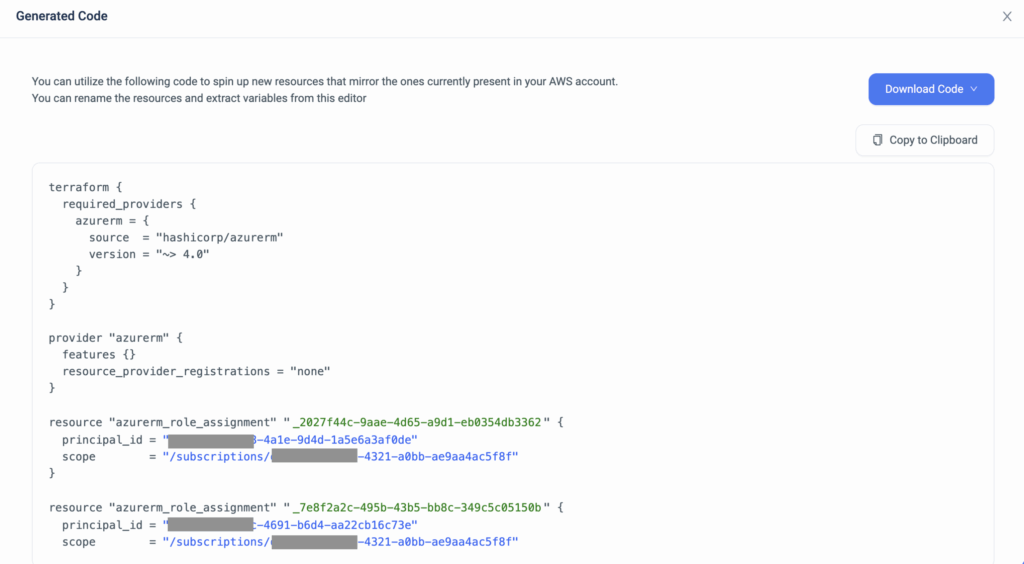
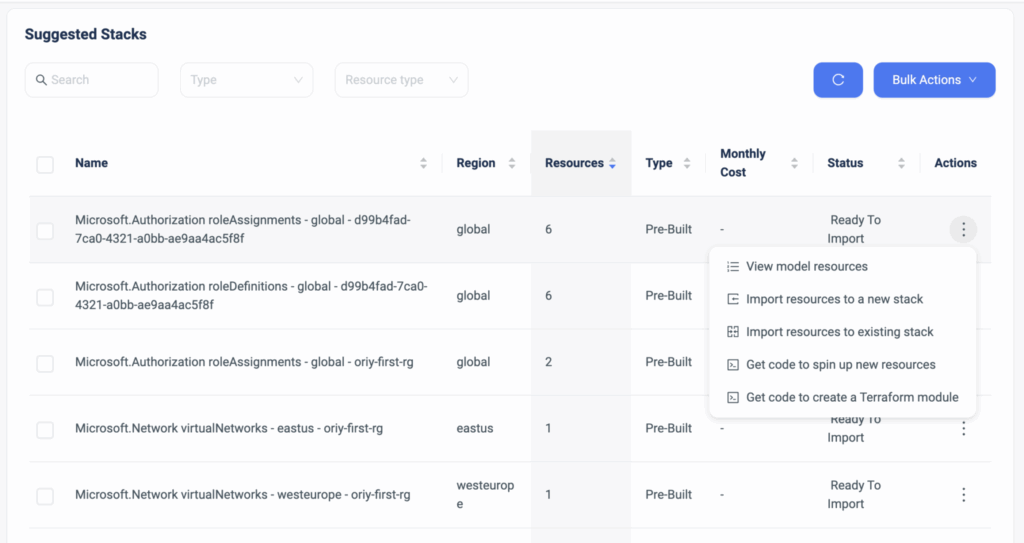
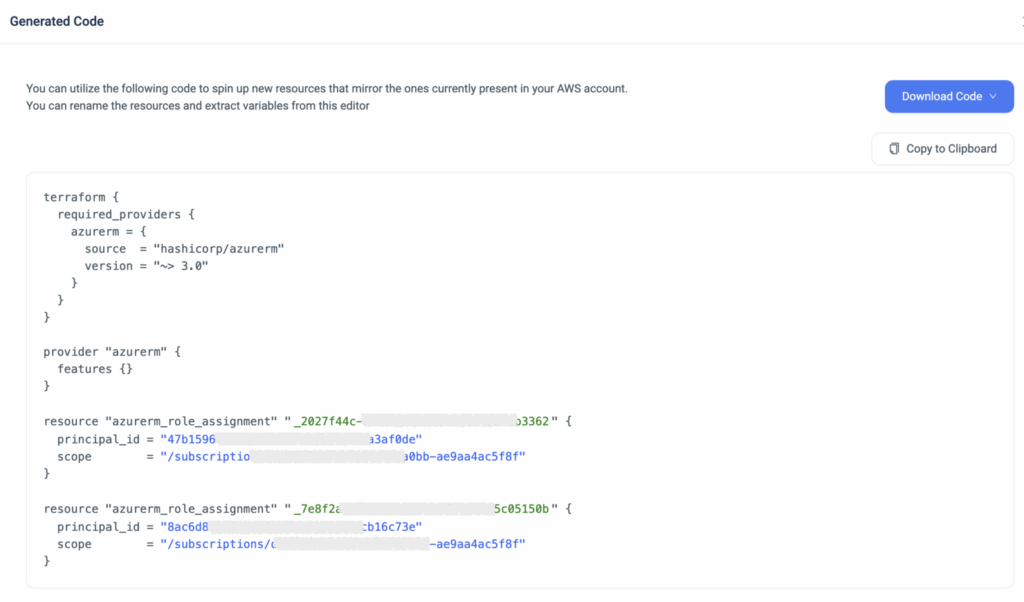
Terraform Import for Datadog resources
Import unmanaged Datadog resources into Terraform with AI-powered code generation.
Datadog Backup Snapshots for Disaster Recovery
Daily backups of all Datadog configurations for fast, reliable recovery.
Governance Posture Insights from Datadog Terraform Integration
Spot compliance gaps and strengthen monitoring governance across environments.
Real-World Example: Bring Datadog Into Terraform
Datadog is often configured manually, outside of version control. That creates visibility and compliance gaps. With ControlMonkey support for Datadog:
- DevOps teams can identify dashboards and monitors not defined in Terraform.
- Automatically generate Terraform code for those unmanaged resources, importing them to Terraform.
- Enable disaster recovery snapshots to ensure rollback options are always available.
This brings governance into the same IaC workflow you use for cloud infrastructure.
How Datadog Terraform Provider Works
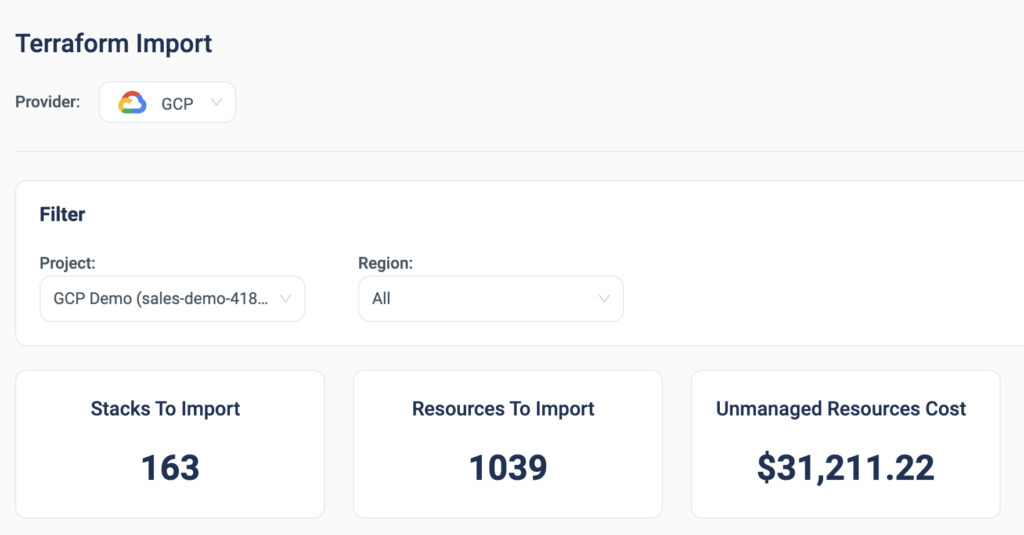
Once connecting your Datadog tenant, ControlMonkey:
- Scans all resources and displays a full inventory.
- Flags resources not managed via IaC.
- Allows you to import them into Terraform in seconds (e.g Terraform Import)
- Enables daily backup snapshots for disaster recovery coverage.
There’s no tagging or scripting required – just visibility and control where it matters.
Stay Ahead with Cloud Governance and Infrastructure Control
By bringing Datadog into ControlMonkey, you benefit from:
- Extend visibility beyond cloud providers to observability tools.
- Reduce risk from untracked, misconfigured, or orphaned monitoring assets.
- Align Datadog configurations with Terraform and OpenTofu policy and workflows.
- Improve your team’s disaster recovery posture.
- Apply infrastructure governance consistently across layers.